Security researchers have discovered a malicious campaign that stores malware in Windows event logs, a technique that has never been publicly described for attacks in the wild.
The technology allowed the attacker to plant fileless malware in the file system using a variety of techniques and modules designed to keep the action as undetectable as possible.
Adding payloads to Windows event logs
After a commercial product equipped with technologies for behavior-based detection and anomaly control detected it as a threat on a customer’s PC, Kaspersky researchers retrieved a sample of the malware. The malware was discovered to be part of a “highly targeted” effort that used a significant number of custom and commercially available tools.
Injecting shellcode payloads into Windows event logs for the Key Management Services (KMS), which is carried out via a proprietary malware dropper, is one of the more intriguing aspects of the assault. According to Kaspersky’s chief security researcher Denis Legezo, this approach was employed “for the first time ‘in the wild’ during the malicious campaign.”
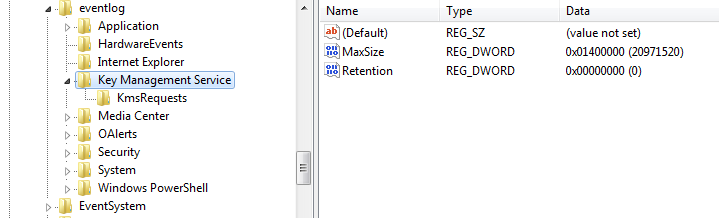
The dropper copies the legal OS error handling programme WerFault.exe to ‘C:WindowsTasks,’ then drops an encrypted binary resource to the same location’wer.dll’ (Windows Error Reporting) allowing DLL search order hijacking to load malicious code. DLL hijacking is a hacking technique that uses insufficient checks in normal programmes to load a malicious Dynamic Link Library (DLL) from an arbitrary route into memory. According to Legezo, the dropper’s goal is to load the disc for the side-loading process and to search the event logs for specific entries (category 0x4142 – ‘AB’ in ASCII).
If no such record is found, it generates 8KB pieces of encrypted shellcode, which are then merged to create the code for the following stager. Soumyadeep Basu, a current intern with Mandiant’s red team, has produced and uploaded source code for injecting payloads into Windows event logs on GitHub, indicating that the new technique investigated by Kaspersky is likely to become more common.
Technically advanced actor
Legezo says the overall campaign “looks remarkable” based on the numerous approaches and modules utilised in the campaign (pen-testing suites, custom anti-detection wrappers, and final stage trojans). “The actor behind the effort is quite sophisticated by itself, or at least has a good set of quite profound commercial tools,” he told BleepingComputer, implying an APT-level foe.
Commercial penetration testing frameworks Cobalt Strike and NetSPI were among the tools utilised in the attack (the former SilentBreak).
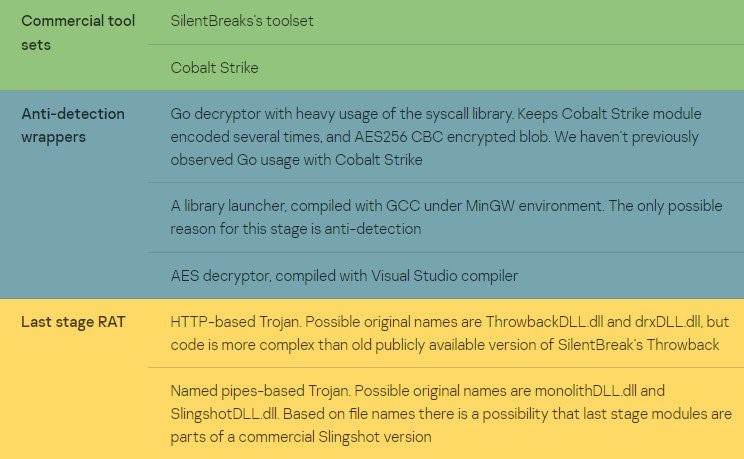
While some of the attack’s components are thought to be unique, the researcher speculates that they could be part of the NetSPI platform, for which a commercial licence was unavailable at the time of testing. For example, two trojans named ThrowbackDLL.dll and SlingshotDLL.dll may be SilentBreak penetration testing framework tools with the identical name.
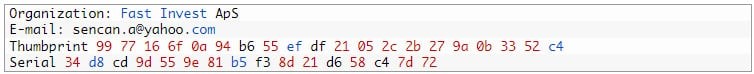
The first stage of the attack was traced back to September 2021, when the victim was duped into downloading a RAR archive from file.io, a file sharing service. The threat actor then distributed the Cobalt Strike module, which was signed with a Fast Invest ApS certificate.
None of the 15 files signed with the certificate were valid.
According to the researcher, the ultimate goal of targeted malware with such last stage functionality is to get some valuable data from the victims in the vast majority of situations. Kaspersky discovered no parallels between the assault and prior efforts linked to a known threat actor while investigating it. Until they can trace the new behaviour to a known adversary, the researchers label it SilentBreak, after the most commonly used tool in the attack.





