APT29, a nation-state actor with ties to Russia, was discovered using Credential Roaming, a “lesser-known” Windows feature. In its attack on an undisclosed European diplomatic entity network.
According to technical writing by Mandiant analyst Thibault Van Geluwe de Berlaere, “the diplomatic-centric targeting is consistent with Russian geopolitical aims as well as traditional APT29 targeting”.
APT29, a Russian espionage organization also known as Cozy Bear, Iron Hemlock. And the Dukes is well-known for its incursions intended to gather information that is consistent with the nation’s strategic goals. It is assumed that the Foreign Intelligence Service is funding it (SVR).
Under the name Nobelium, a threat cluster that was in charge of the massive supply chain compromise through SolarWinds software. In December 2020, some of the antagonistic collective’s online activities are monitored in the open. During the early 2022 period, when APT29 was active inside the target network, several LDAP requests with anomalous attributes were made against the Active Directory system. According to the Google-owned threat intelligence and incident response company.
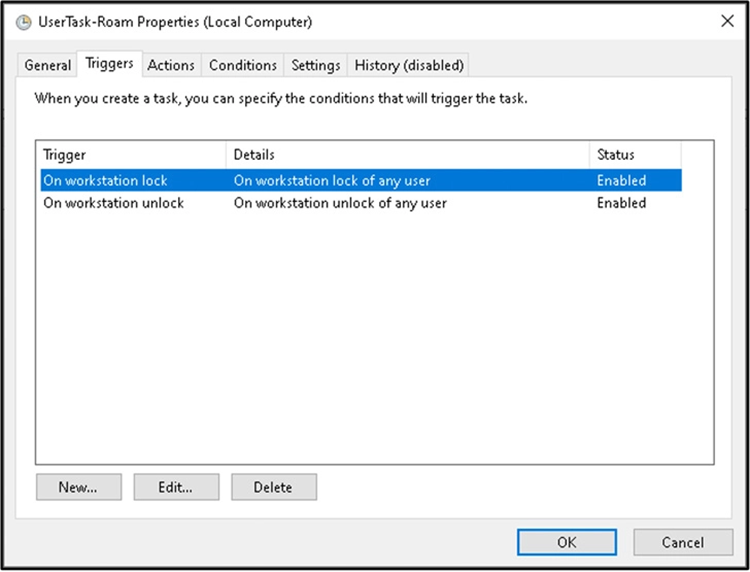
Credential Roaming is a feature that was added to Windows Server 2003 Service Pack 1 (SP1). The service enables users to securely access their credentials from various workstations in a Windows domain.
Further investigating the system’s inner workings led Mandiant to the identification of an arbitrary file write vulnerability that a threat actor may exploit to execute remote code in the context of the logged-in victim.
The Final Remarks
Microsoft fixed the flaw, identified as CVE-2022-30170, as part of Patch Tuesday updates that were distributed on September 13, 2022. The company emphasized that exploitation required a user to log in to Windows.
An attacker who exploited the vulnerability may gain remote interactive login access to a machine where the victim’s account would not typically hold such privilege.
Mandiant advised enterprises to apply the September 2022 fixes to safeguard themselves against the vulnerability. This says the research “provides insight into why APT29 is aggressively querying the associated LDAP attributes in Active Directory”.





