The Global Cybersecurity Outlook 2022 report has revealed that ransomware attacks have increased as such by 151% in 2021. There were nearly 270 cybersecurity…
Cybersecurity
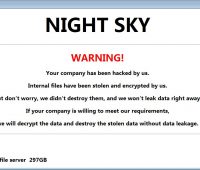
Night Sky, the new ransomware
In the cyber security area, there is new ransomware to keep an eye on called as, ‘Night Sky’. This was first spotted by Malware…
Box account’s 2-factor authentication system can be circumvented
Cybersecurity researchers have revealed information on a now-patched bug in Box multi-factor authentication (MFA). The bug could be exploited to circumvent SMS-based login verification.…
UniCC the largest dark web market for stolen cards, shuts down
The largest dark web marketplace for stolen credit and debit cards, UniCC has stated that it’s shutting down its operations. Since 2013, UniCC has…
Critical vulnerability in 3 WordPress Plugins impacts 84,000+ websites
Researchers have uncovered a critical vulnerability plaguing three different WordPress plugins. These plugins can affect more than 84,000 websites and may be exploited by…
Crypto Mining attacks use evolved version
A crypto mining campaign, which has been active, has developed its method to avoid detection. The threat actors have evolved their attack method to…
‘Double Feature’: researchers dived in tool
Cybersecurity researchers have offered insight into a system known as Double Feature. The system tracks different stages of post-exploitation originating from the DanderSpiriz—a full-featured…
Web application attacks substantial rise
Imperva Research Lab’s study concluded that web application attacks are rising, on average, by 22% each quarter. The study examined nearly 4.7 million web…
Data Breach in West Virginia Hospital
Hackers targeted a hospital system in West Virginia; the attackers used a phishing attack for a data breach from the hospital’s system. Monongalia health…
Vulnerabilities let hackers control directory
Microsoft has pushed users to patch two security vulnerabilities in Active Directory domain controllers that it released in November. Microsoft has become active after…