ConnectWise, a provider of IT service management software, has published software fixes to address a serious RCE vulnerability in Recover and R1Soft Server Backup Manager (SBM).
The problem is referred to as a neutralization of Special Elements in Output Used by a Downstream Component. That could be exploited to cause the execution of remote code or the revealing of private data.
Versions Recover v2.9.7, R1Soft SBM v6.16.3, and earlier, are also compromised by the significant issue, according to ConnectWise’s advice.
The ZK open-source Ajax web application framework contains a rce vulnerability called CVE-2022-36537 that allows upstream authentication to be bypassed. This vulnerability was first addressed in May 2022.
Customers were urged to update to SBM v6.16.4, which was released on October 28, 2022, saying that “Affected ConnectWise Recover SBMs have automatically been upgraded to the newest version of Recover (v2.9.9).”
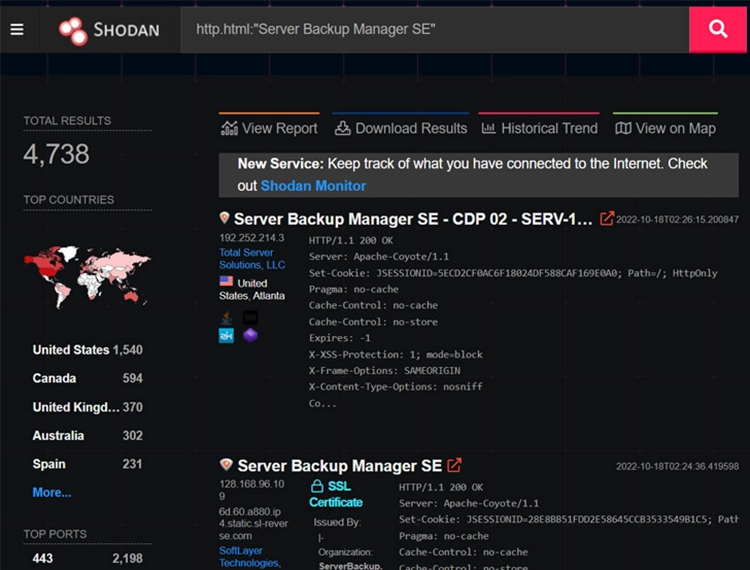
A supply chain risk for businesses by upwards of 5,000 vulnerable server manager backup instances, according to cybersecurity firm Huntress.
Despite the fact that there is no proof of active exploitation of the vulnerability in the wild, John Hammond. And Caleb Stewart of Huntress demonstrated how it could be exploited to bypass authentication. This gained remote code execution on SBM and spread LockBit 3.0 ransomware to all downstream endpoints.
The researchers emphasized that the upstream ZK vulnerability affects all applications using an unpatched version ZK framework, not just R1Soft.
“While the access a hacker can obtain via this authentication bypass vulnerability is specific to the programme being attacked. There is a significant risk that other apps could be adversely affected in a manner similar to R1Soft Server Backup Manager.





