VMware’s virtualization software has been revealed to be used by threat actors to implant never-before-seen post-compromise implants. The implants allow them to take control of compromised systems while avoiding detection.
It affects VMware ESXi, Linux vCenter servers, and Windows virtual machines, giving attackers continued access to the hypervisor. The ability to run arbitrary commands, according to Google’s Mandiant threat intelligence group.
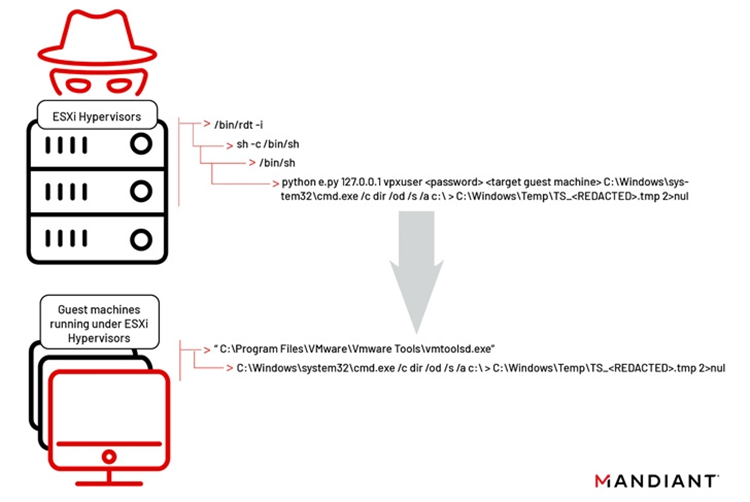
According to the cybersecurity vendor, two implants known as VIRTUALPITA and VIRTUALPIE were secretly installed on the ESXi hypervisors. As part of the hyperjacking attacks using malicious vSphere Installation Bundles (VIBs).
Researchers from Mandiant Alexander Marvi, Jeremy Koppen, Tufail Ahmed, and Jonathan Lepore wrote in a thorough two-part report. “It is important to highlight that this is not an external remote code execution vulnerability; the attacker needs admin-level privileges to the ESXi hypervisor before they can deploy malware”.
There is no proof that ESXi servers were breached using a zero-day vulnerability. However, the usage of trojanized VIBs, a standard for software packages that makes it easier to distribute software and manage virtual machines, indicates a new degree of sophistication.
According to Marvi, the threat actor previously gained access to the victim environments via attack methods unrelated to VMware. They discovered and stole the VMware administrator credentials, then used them to enter into the ESXi servers and distribute the malicious VIB files. This was done using their established network access.
According to VMware, “This malware differs in that it enables remaining persistent and covert, which is compatible with the objectives of more prominent threat actors. And APT organizations target important institutions with the intention of lingering unnoticed for a while.
The Issues
While VIRTUALPITA can run commands and do file uploads and downloads, VIRTUALPIE is a Python backdoor that supports reverse shell functionality, command line execution, and file transfers.
A malware sample named VIRTUALGATE, a C-based utility programme that launches an embedded payload capable of leveraging VMware’s virtual machine communication interface (VMCI). The sockets have to perform instructions on a guest virtual machine from a hypervisor host have also been found in Windows guest virtual machines.
Although less than 10 enterprises are claimed to have used the virus. Marvi claims the number is expected to rise as more businesses check their VMware infrastructure. It’s unclear at this moment whether the attacks are focused on a particular industry due to the low infection level.
Mandiant also cautioned that the campaign’s use of virtualization software to get around typical security measures. This represents a new attack surface that other hacking groups are likely to adopt.
The intrusions have been linked to an unclassified, emerging threat cluster with the codename UNC3886. The motivation is most likely espionage-related given the intrusions’ highly targeted nature. It also gave a low degree of confidence to the claim that UNC3886 is connected to China.





