Hackers are distributing fake shopping apps to steal Malaysian users’ banking information.
Since at least November 2021, threat actors have been distributing malicious applications disguised as seemingly harmless shopping apps to target customers of eight Malaysian banks.
The attacks involved the creation of fraudulent but legitimate-looking websites in order to trick users into downloading the apps, according to a report.
Copycat websites impersonated cleaning services such as Maid4u, Grabmaid, Maria’s Cleaning, Maid4u, YourMaid, Maideasy, and MaidACall, as well as a pet store called PetsMore, all aimed at Malaysian users.
Threat actors use these bogus e-commerce applications to phish for banking credentials, according to ESET. In addition, the apps forward all SMS messages received by the victim to the malware operators if they contain 2FA codes sent by the bank.
The targeted banks include Maybank, Affin Bank, Public Bank Berhad, CIMB bank, BSN, RHB, Bank Islam Malaysia, and Hong Leong Bank.
The websites, distributed through Facebook ads, urge visitors to download what the attackers claim to be are Android apps available on the Google Play Store, but in reality, redirect them to rogue servers under their control.
It’s worth noting here that the attack hinges on the prerequisite that the potential victims enable the non-default “Install unknown apps” option on their devices for it to succeed. What’s more, five of the abused services don’t even have an app on Google Play.
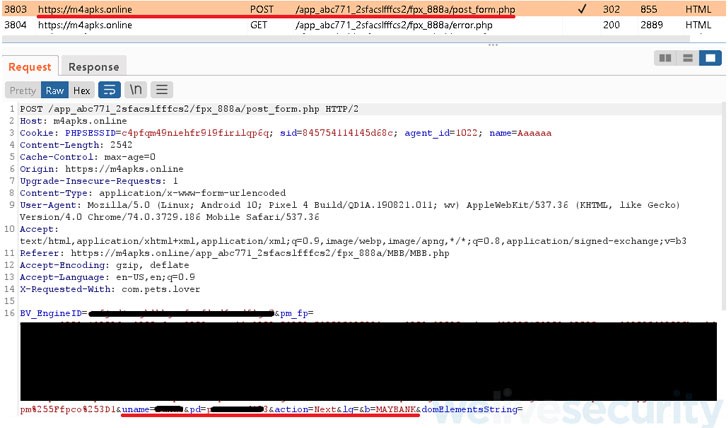
Once launched, the apps prompt the users to sign in to their accounts, allowing them to place fake orders, following which options are presented to complete the checkout process by including a fund transfer from their bank accounts.
“After picking the direct transfer option, victims are presented [with] a fake FPX payment page and asked to choose their bank out of the eight Malaysian banks provided, and then enter their credentials,” ESET malware researcher Lukáš Štefanko said.
The ultimate goal of the campaign is to steal the banking credentials entered by the users and exfiltrate it to the attacker-controlled server, while displaying an error message that the entered user ID or password is invalid.
In addition, the fake apps are engineered to access and transmit all SMS messages received by the users to the remote server in the event the bank accounts are secured by two-factor authentication.
“While the campaign targets Malaysia exclusively for now, it might expand to other countries and banks later on,” Štefanko said. “At this time, the attackers are after banking credentials, but they may also enable the theft of credit card information in the future.”
Reference: https://thehackernews.com/2022/04/hackers-distributing-fake-shopping-apps.html





