After a year-long operational sabbatical, the Brazilian threat actor Prilex has returned with sophisticated and intricate Point-of-Sale Malware to steal money through fraudulent transactions.
According to Kaspersky researchers, “The Prilex gang has demonstrated a high level of expertise about credit and debit card transactions. As well as how software used for payment processing works”. Because of this, attackers are able to continually improve their tools and carry out their attacks by finding a means to get around permission restrictions.
The cybercrime group first appeared on the scene in the South American country with ATM-focused malware attacks. It gives the ability to break into ATMs to perform jackpotting. Jackpotting is a type of attack that aims to disburse cash illegally. And clone thousands of credit cards to steal money from the targeted bank’s customers.
Since then, Prilex’s strategy has changed to make use of point-of-sale (PoS) software procedures to intercept and alter communications with electronic devices. These include PIN pads, which are used to enable debit or credit card payments.
The operators, who have been active since 2014, are also skilled at executing EMV replay attacks. In which the transaction fields of a legal EMV-based chip card transaction are modified and replayed to a payment processor like Mastercard.
It takes a highly-targeted attack with a social engineering component to infect a computer that has PoS software installed in order to use the virus.
The researchers stated that “a target business may receive a call from a ‘technician’ who claims that the business has to upgrade its PoS software”. The phoney technician might physically visit the target or ask the victims to install AnyDesk. So the ‘technician’ can install the virus remotely.
The Techniques
However, the most recent versions discovered in 2022 show an important distinction. The replay attacks have been replaced with a different method to illegally withdraw money utilizing cryptogram. They are produced by the victim’s card during the in-store payment procedure.
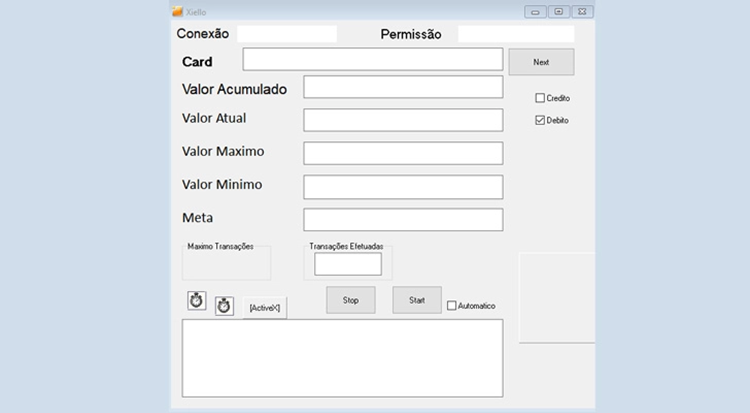
The technique, known as GHOST transactions, consists of a stealer component that records all communications. They made while the transaction is being processed between the PoS software and the PIN pad used to read the card.
Following transmission to a command-and-control (C2) server. This enables the threat actor to conduct transactions using a false PoS device. The device is registered in the name of a fictitious business.
Now, it’s important to note that every time a transaction is made, EMV chip cards use a cryptogram to encrypt cardholder data. This lowers the possibility of fraudulent purchases by validating the card’s identification and the card issuer’s consent.
The GHOST attack asks for new EMV cryptograms that are used to carry out fraudulent transactions. In contrast to previous versions of Prilex which got around these security measures by keeping an eye on the transaction to obtain the cryptogram. And conduct a replay attack using the gathered “signature.”
A backdoor module that is designed to debug the PoS software behavior. Making changes instantly is also incorporated into the malware. Other backdoor commands give it permission to kill processes and initiate and stop screen captures.
According to the researchers, Prilex “deals directly with the PIN pad hardware protocol instead of using higher level APIs. Does real-time patching in target software, hooks operating system libraries, messes with replies, communications, and ports. And switches from a replay-based attack to generate cryptograms for its GHOST transactions. Even from credit cards protected with CHIP and PIN technology.”





