Cybercriminals are marketing a new Android spyware called “Hook,” claiming it can remotely control mobile phones in real-time using VNC (virtual network computing). Hook A new Android spyware allows hackers to manipulate your phone remotely.
The Ermac developer Android banking trojan costs $5,000/month and aids threat actors in stealing passwords from over 467 banking. And cryptocurrency apps via overlapping login screens are promoting the new infection.
Despite having several additional functionalities over Ermac, Hook’s creator claims that the new malware was entirely created from scratch. However, researchers at ThreatFabric doubt this assertion and find significant code parallels between the two families.
Also, read 3,000,000 New Android Malware Downloads From Google Play
According to ThreatFabric, Hook is still a trojan horse because it uses a large portion of Ermac’s code base. In addition, it has several extra portions present in the previous strain and shows that it reused code frequently.
Dangerous Android malware
Regardless of where it came from, Hook advanced Ermac providing features that make it a major threat to Android users.
Hook differs from Ermac in that it adds WebSocket connectivity as a new feature in addition to the HTTP traffic that Ermac only uses. AES-256-CBC is still being used to encrypt the network traffic.
The “VNC” module, which enables threat actors to engage with the hijacked device’s user interface in real time, is the addition that stands out the most.
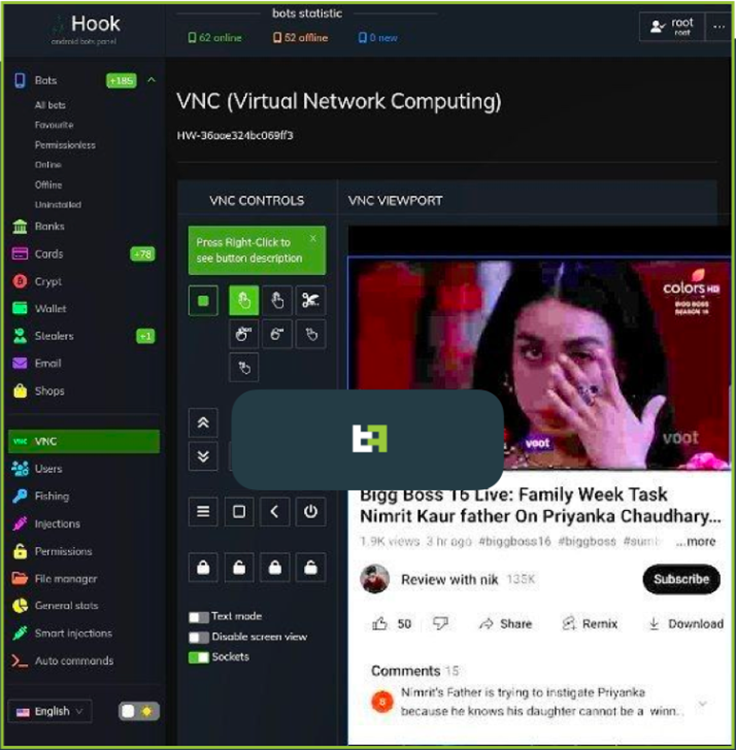
Any activity, including the exfiltration of personally identifiable information and financial transactions, is now possible for Hook’s operators to carry out.
With this feature, ThreatFabric cautions Hook “joins the ranks of malware family that can complete DTO, and complete a full fraudulent chain, from PII exfiltration to payment, with all the intermediate phases, without the requirement of additional channels.”
The primary selling point for Android bankers is the difficulty in operation for fraud score engines to identify.
Also, read 2,000,000 Android malware applications have been found on Google Play.
The problem is that for Hook’s VNC to function, it needs access to the Accessibility Service. This may be challenging on Android 11 or later.
In addition to those mentioned above, a “File Manager” instruction transforms the virus into a file manager, enabling threat actors to download particular files of their choice and acquire a list of all items stored on the device.
Another noteworthy command discovered by ThreatFabric relates to WhatsApp, enabling Hook to record all communications sent and received through the well-known IM software. And even enabling administrators to send messages using the victim’s account.
Hook operators can now track the victim’s precise location by exploiting the “Access Fine Location” permission. Thanks to a new geolocation tracking technology.
Worldwide Targeting
Hook’s target banking applications impact users in the US, Spain, Australia, Poland, Canada, Turkey, the UK, France, Italy, and Portugal.
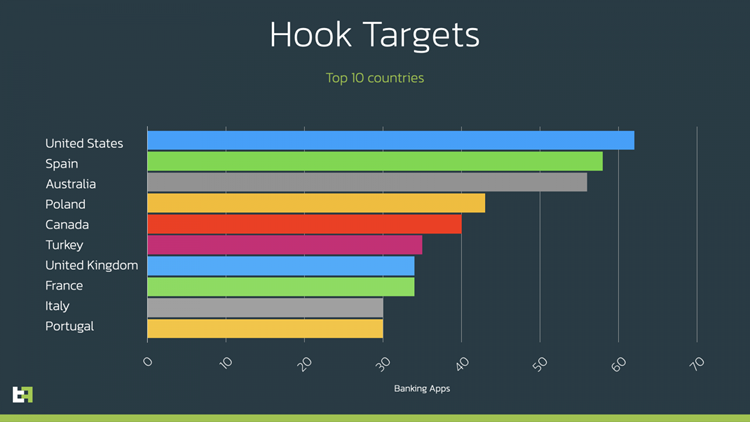
But it’s important to remember that Hook’s global targeting range encompasses the entire planet. For those who are interested, ThreatFabric has a list of all the apps that Hooks targets in the study’s appendix.
The Hook is currently offered as a Google Chrome APK with the package names. These include “com.lojibiwawajinu.guna,” “com.damariwonomiwi.docebi,” “com.damariwonomiwi.docebi,” and “com.yecomevusaso.pisifo,” but this could alter at any time.
You should install apps from the Google Play Store provided by your employer to prevent getting infected with Android malware.





