TAP Air Portugal data leaks by a gang going by the name Ragnar Locker in late August. The firm reportedly declined to help the attackers, leading to a larger release this week.
Initially, the group made available about 115,000 client datasets that they had obtained by abusing a flaw in the carrier’s IT system. But there are now reportedly ten times as many.
In addition to the customer data, they now made available private company records concerning partners, staff, and contract information with other carriers.
TAP had never truly admitted to being hacked; instead, it had described the situation as “system instability.”
Several publications and information security websites first revealed the intrusion at the beginning of September.
Earlier Story:
According to the Ragnar Locker ransomware group, a hack on TAP Air Portugal, the national airline of Portugal, resulted in the theft of passenger data.
When TAP tweeted that it had stopped the intrusion before the threat actor could obtain any customer data. The incident was first made public on August 26.
A cyberattack that was directed toward TAP has since been stopped. The integrity of operations is ensured. There are no facts that allow us to draw the conclusion that consumer data has been accessed improperly. There is still some volatility with the website and app. We appreciate your patience, the business added.
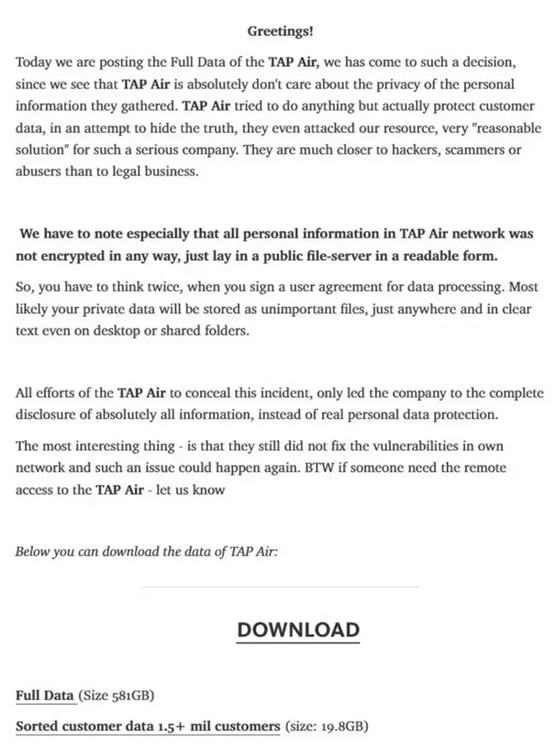
However, the Ragnar Locker ransomware group bragged on their leak’s website on August 31 that the airline’s computers had actually been compromised and that user data had been stolen.
The threat actor also made an effort to embarrass TAP by warning that the data breach could lead to the largest lawsuit in history and implying that the incident affected the personal information of at least hundreds of thousands of TAP users.
The gang also published a screenshot that purportedly showed data theft during the cyberattack. It appears that the screenshot contains names, addresses, email addresses, phone numbers, company IDs, travel details, nationality, gender, and other personal data.
The TAP
TAP did not mention data loss in an advisory it posted on its website on September 1, but it did let users know that “the website and the app are still recording some difficulties.”
All is well thus far. One would have assumed that would be the end of it as we haven’t heard anything further for the past three weeks. But it appears that the hackers have started round two.
According to a story from Expresso Portugal published today, TAP refused to accept the hackers’ demands for ransom money. Therefore 1.5 million client records and further information about the organization are now available on the black web.
The Organization
The cybercriminal organization Ragnar Locker made the threat it had been threatening. On Monday it released 581 GB of data it claims links to 1.5 million TAP users. The Ragnar Lockers also promise that they will always have access to TAP’s computer systems in a message posted on the Dark Web. In addition to the tables containing addresses, phone numbers, and customer names. The data breach also includes identification documents for individuals who appear to be TAP employees or partners. As well as private contracts with various businesses and connections to other airlines, according to the Express, which accessed the files.
The most intriguing aspect is that TAP has not yet addressed the network’s inherent vulnerabilities, meaning that another occurrence of this nature might occur. By the way, at the end of the statement Ragnar Locker just posted on the Dark Web, it says, “If anyone requires remote access to TAP Air [sic], let us know.
The Issues
To fix the issues that caused the material to leak, TAP has been collaborating with the Judiciary Police, the National Cybersecurity Center, and Microsoft. Expresso contacts TAP, who says that “the incident contains at an early stage, before inflicting damage to operational processes. Thanks to cybersecurity systems and the fast action of the in-house Information Technology team.
TAP reiterates that operations are running smoothly while avoiding going into specifics about the claim that hackers had remote access. TAP continues, “Therefore, we will continue to take all required actions.”
Just over a week ago, the organization that specializes in demanding ransom payments to unlock infected computers published on the Dark Web data on 115 000 customers and private information from TAP professionals as proof of the files it allegedly obtained by exploiting flaws in the carrier’s computer networks.
Expresso discovered that TAP rejected the cybercriminals’ suggestion and refused to negotiate the payment of a ransom to stop the publication of the data. This is a common form of retaliation when businesses refuse to pay a ransom to unlock infected computers because they have backup copies that enable quick system replacement.
The Circumstances
It is difficult to determine the best course of action in this situation and impossible to do so without knowing the circumstances. On the one hand, paying a ransom is never a smart idea because it invites more forms of extortion. Who can ensure that the hackers are erasing the data they stole from TAP’s systems (very unlikely)? Typically, law enforcement advises impacted parties not to pay any ransom.
Although I don’t want to condone or defend this criminal action. It appears that TAP hasn’t tried to fix its security flaws since it first learned of the intrusion.
Both personal and corporate data are now in the open since the hackers simply released all the data on the dark web. After realizing the company wouldn’t pay and was making no progress in closing the gap.
Conclusion
If you use TAP Air Portugal, you might want to take a close look at the passwords and other private data linked to your TAP accounts. The data such as the loyalty login and online portal. Change the passwords on the bench because of the hacker’s criminal activity. And TAP’s negligence in maintaining database security has certainly compromised your information.
Given the fairly careless attitude TAP demonstrated here. This resulted in extremely large fines, as businesses like British Airways, have already had to experience.





