The decentralized Interplanetary Filesystem (IPFS) network is being used by a variety of phishing attempts to host malware, phishing kit infrastructure, and support other attacks.
According to data released with The Hacker News by Cisco Talos researcher Edmund Brumaghin. Hosting many malware families within IPFS and retrieved during the earliest stages of malware attacks. Numerous Cyber Attacks Using IPFS Decentralized Network Seen.
In July 2022, Trustwave SpiderLabs discovered over 3,000 emails with IPFS phishing URLs as an attack vector. Labeling IPFS as the new “hotbed” for hosting phishing sites. These findings are comparable to those in the current study.
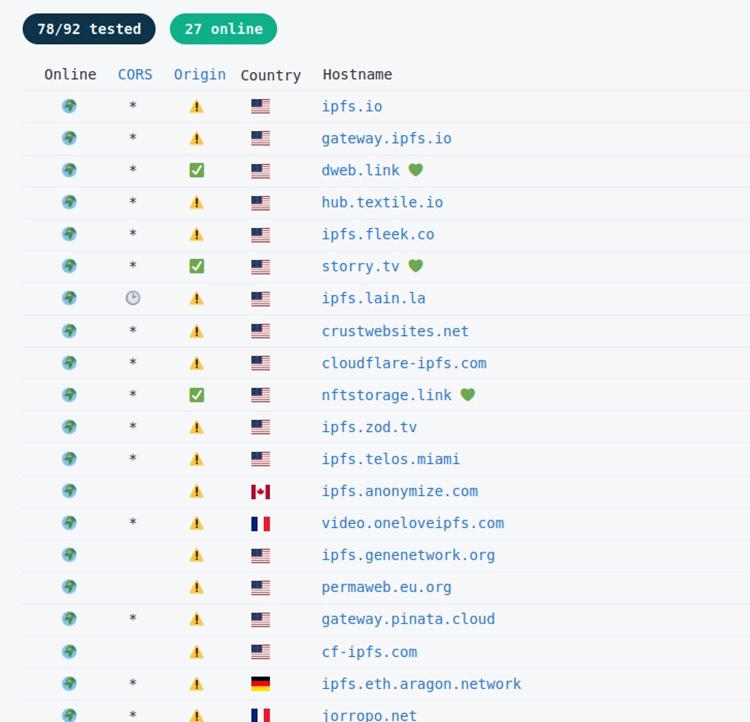
IPFS is a technology that has a double-edged sword in that it is resistant to both censorship and takedowns. It is based on a peer-to-peer (P2P) network that replicates content across all involved nodes so that requests for the resources can still be fulfilled by other systems even if the content is withdrawn from one machine.
This renders it vulnerable to exploitation by criminals wishing to host malware that can withstand efforts by law enforcement to compromise their attack infrastructure, as was the case with Emotet last year. Brumaghin earlier told in August 2022 that “IPFS is now being abused by a number of threat actors who are utilizing it to host malicious data as part of phishing and malware distribution campaigns.”
The Vulnerability
Included in this is Dark Utilities, a command-and-control (C2) framework that advertises itself as a mechanism for adversaries to get access to remote systems, and engage in DDoS attacks. And engage in bitcoin mining, with the platform’s offered payload binaries being hosted on IPFS. Numerous Cyber Attacks Using IPFS Decentralized Network Seen.
Furthermore, phishing efforts are designed to steal passwords and disseminate a variety of malware. These include Agent Tesla, reverse shells, and data wipers. And an information thief known as Hannabi Grabber has used IPFS to serve bogus landing pages.
In one malspam delivery chain described by Talos, an email claiming to be from a Turkish financial institution instructed the recipient to open a ZIP file attachment, which when opened served as a downloader for an IPFS network-hosted, obfuscated copy of Agent Tesla.
The Final Thoughts
The malicious software causes destruction and manifests itself as a batch file that deletes all directory contents and removes backups. A Python-based malware programme called Hannabi Grabber collects private data from the infected host, including screenshots. And browser information, and sends it to a Discord Webhook.
The most recent development indicates a rise in the use of legitimate services by attackers to host malicious content or route users to it. This includes Discord, Slack, Telegram, Dropbox, Google Drive, AWS, and several more. Phishing is one of these profitable key initial access vectors.
According to Brumaghin, “this activity to continue to grow as more threat actors realize that IPFS can facilitate bulletproof hosting. It is resistant to content moderation and law enforcement activities and introduces problems for organizations trying to detect. And defend against attacks that may leverage the IPFS network.”





