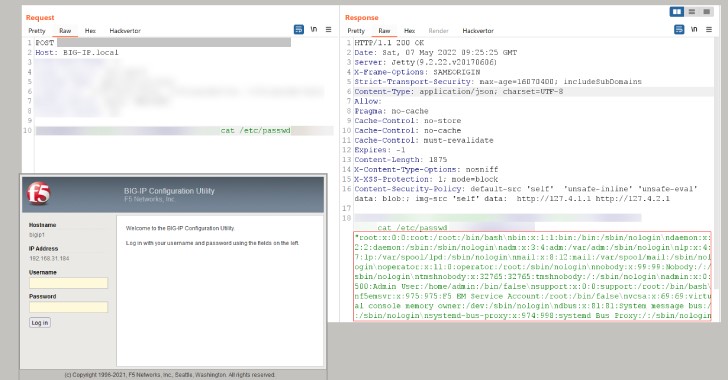
Security researchers are warning that they were able to construct an exploit for a serious remote code execution vulnerability affecting F5’s BIG-IP family of devices just days after the company provided patches for the flaw.
The weakness, which has been assigned the number CVE-2022-1388 (CVSS 9.8), is related to an iControl REST authentication bypass that, if properly exploited, might lead to remote code execution, allowing an attacker to obtain initial access and take control of an affected machine.
This might include everything from cryptocurrency mining to the deployment of web shells for follow-on operations like data theft and ransomware.
Positive Technologies, a cybersecurity firm, tweeted on Friday, “We have replicated the fresh CVE-2022-1388 in F5’s BIG-IP.” “Patch right away!”
The following versions of BIG-IP products are affected by the critical security vulnerability:
16.1.0 – 16.1.2
15.1.0 – 15.1.5
14.1.0 – 14.1.4
13.1.0 – 13.1.4
12.1.0 – 12.1.6
11.6.1 – 11.6.5
Versions 17.0.0, 16.1.2.2, 15.1.5.1, 14.1.4.6, and 13.1.5 all have fixes. Users who rely on firmware versions 11.x and 12.x will not receive security updates, and should consider updating to a later version or using the solutions –
The self IP address is used to block iControl REST access.
Through the management interface, disable iControl REST access, and
Make changes to the BIG-IP httpd settings.
Last month, Australia, Canada, New Zealand, the United Kingdom, and the United States issued a joint statement warning that “threat actors aggressively targeted recently reported critical software vulnerabilities against broad target sets, including public and commercial sector enterprises globally.”
Malicious hacking crews are expected to follow suit now that the F5 BIG-IP issue has been discovered to be straightforward to attack, making it critical that impacted firms apply the updates as soon as possible.