Targeting VMware ESXi virtual computers, Royal Ransomware is the most recent ransomware operation to add capabilities for encrypting Linux devices to its most recent malware strains.
Similar Linux ransomware encryptors have been made available by numerous different gangs, including Black Basta, LockBit, BlackMatter, AvosLocker, REvil, HelloKitty, RansomEXX, and Hive.
Will Thomas of the Equinix Threat Analysis Center (ETAC) identified the new Linux Royal Ransomware strain, which uses the command line to execute.
Additionally, it has support for several flags that will provide the ransomware developers some degree of control over the encryption process:
- -stopvm > stops all running VMs so they can be encrypted
- -vmonly – Only encrypt virtual machines
- -fork – unknown
- -logs – unknown
- -id: id must be 32 characters
All files on the VM that the ransomware has encrypted will have the.royal u extension appended to them.
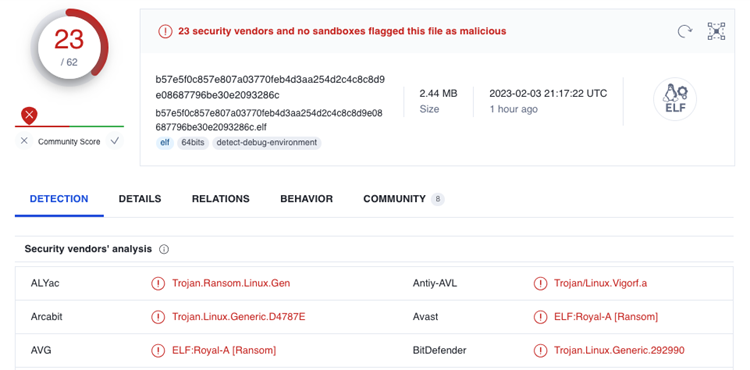
While some anti-malware programmes had trouble detecting Royal Ransomware samples with additional targeting capabilities, 23 out of 62 malware scanning engines on VirusTotal are now able to do so.
Who is Royal Ransomware?
A private operation called Royal Ransomware was founded by seasoned threat actors who had previously worked for the Conti ransomware organization.
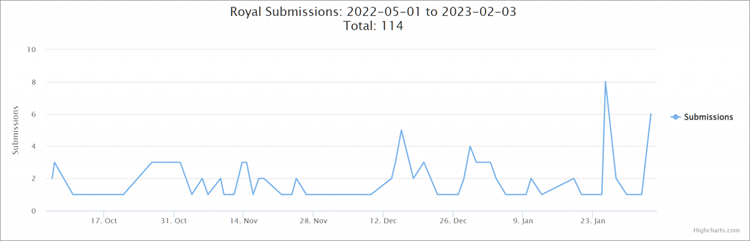
Royal began to increase its malicious activity in September, months after it was initially discovered in January 2022.
They switched from employing encryptors from other operations, like BlackCat, to using their own, beginning with Zeon which released ransom notes resembling those produced by Conti.
The organization changed its name to “Royal” in the middle of September and started using a new encryptor in assaults that creates ransom notes with the same name.
The gang encrypts the enterprise network systems of their targets and then demands ransom payments that range from $250,000 to tens of millions.
The U.S. Department of Health and Human Services (HHS) issued a warning in December about ransomware attacks using the Royal code that target businesses in the Healthcare and Public Healthcare (HPH) sector.
Now, the majority of ransomware outbreaks target Linux.
The shift by ransomware organizations to target ESXi virtual machines fits with a pattern where businesses are switching to VMs because they offer better device control and much more effective resource handling.
The ransomware operators encrypt several servers with a single command after delivering their payloads on ESXi hosts.
Wosar previously stated that “the reason why most ransomware gangs built a Linux-based variant of their ransomware is to target ESXi particularly.”
According to a Lansweeper analysis, tens of thousands of VMware ESXi servers that were available online reached their end of life in October.
Final Things
From this point forward, these systems will only receive technical assistance and no security updates, leaving them vulnerable to ransomware attacks.
A new malware strain known as ESXiArgs was employed to scan for and encrypt unpatched servers in a huge campaign targeting ESXi devices globally this Friday, putting things in perspective and demonstrating just how vulnerable such servers are to attacks.
A Shodan search revealed that over 100 servers were hacked worldwide in just a few hours due to these attacks.