Since Google announced its campaign to auto-enrol users for 2-step verification last year, Google has auto-enrolled more than 150 million users in 2 step-verification.…
Cybersecurity
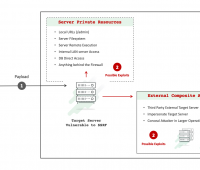
SSRF flaws created in multiple apps via Google Drive integration errors
Execution flaws in Google Drive integrations created server-side request forgery (SSRF) vulnerabilities in a mixture of applications, a security researcher has disclosed. This included…
Attackers can Take Over Computers through PowerPoint Files
Attackers use socially engineered emails with .ppam file attachments that hide malware that can rewrite Windows registry settings on targeted machines. The attacker used…
Hackers target European Oil ports
Belgian prosecutors are investigating the hacking of oil facilities in the country’s ports, including Antwerp—Europe’s second-biggest port after Rotterdam. In Germany, prosecutors said they…
SolarMaker malware evolved to sustain in hacked systems
Threat actors regularly work on their attack strategy and defence measures to beat the protective measures. Solarmaker information stealer and backdoor operators have been…
Emsisoft’s Deadbolt decryption tool is available
Deadbolt ransomware has got a decryption key after a few days it first appeared. However, the threat actors must provide a decryption key for…
Secure keys generated by researchers using natural silk fibres and the keys offered a strong authentication
At South Korea’s Gwangju Institute of Science and Technology (GIST), researchers have used natural silk fibres, silk fibres that are made from domesticated silkworms…
Microsoft mitigates several attacks in 2021
This week Microsoft said it prevented several denial-of-service (DDoS) attacks targeting its customers in 2021. Three of the attacks exceeded 2.4 terabits per second…
Cybersecurity trends in 2022
Every day, new technologies are disrupting and improving our lives, businesses, industries, and in the larger landscape, the conveniences and efficiencies we once thought…
Log4j vulnerability targets SolarWinds, ZyXEL devices
SolarWinds and ZyXEL devices are being attacked by cybercriminals who are searching for Log4jShell vulnerability aka log4j vulnerability. The devices are known to contain…