In an effort to stop hackers and emphasize America’s tight ties with Kyiv, the U.S. military publicly disclosed a number of malware indications in response to a campaign of cyberattacks against Ukraine.
Twenty novel indicators of malware infections were released on Wednesday by U.S. Cyber Command in collaboration with the Ukrainian Security Service.
“To improve our collective cybersecurity, our Ukrainian partners actively share malicious behaviour they discover with us, just as we do with them. Our two countries continue to have a solid collaboration in cybersecurity, “the US Cyber Command claims.
The military leadership has acknowledged collaborating with Ukrainian Cyber Command to find weaknesses and catch hackers. Through the delivery of weapons and humanitarian aid, the United States has supported Ukrainian defence. President Joe Biden said in June that the nation of Eastern Europe would get an additional $1 billion in security support. This was the sixth shipment of American weapons since August 2021.
Following Russia’s invasion in February, Ukrainian cyberspace was put on high alert as defences prepared to fend off an array of wipers and other digital attacks (see: Major Takeaways: Cyber Operations During Russia-Ukraine War).
Both the victims of the virus as well as the threat actor behind the indicators are kept secret by the authorities.
In order to participate in the information dump, Mandiant, a cybersecurity company with connections to the U.S. military, published a study that went in-depth on some of the disclosed indicators of compromise.
Researchers at Mandiant described two distinct initiatives, one from a threat organisation that the company believes is connected to the government of Belarus, an ally of Russia, and the other that is at least partially funded by Moscow.
Both gangs use malicious papers that pose as safety or humanitarian advice to trick their victims into opening them.
UNC2589 Operations
One threat organization, known as UNC2589, supports Russian government objectives and has been gathering espionage in Ukraine. Other businesses, such as Saintbear and TA471, track it under various names.
Mandiant suspects that this organization was responsible for pre-invasion malware attacks on Ukrainian government websites in January (see: Teardown: Fake Ransomware Targeting Ukrainian Government).
Mandiant claims that although “we suspect UNC2589 acts in Favour of Russian government purposes, we have not identified evidence to link it definitively.” The threat actor sends attachments that show up in inboxes as messages received from valid but compromised accounts or from his own accounts in order to obtain access to machines. The COVID-19, the Ukrainian government, the continuing conflict, or even Bitcoin are among the themes used as lures.
Malicious document macros, Windows Control Panel files, and.zip compression files are examples of payloads. The majority of the IP addresses in its command-and-control network are Russian.
When the threat group’s malware is executed, it establishes persistence by programming it to launch every time a user login into the infected machine. Then it downloads and runs two more files, one named Graphsteel to steal information and another called Grimplant to create a backdoor. The latter checks credentials from many browsers, including Chrome, Firefox, and Internet Explorer. Additionally, it tries to gather mail information if it discovers a Thunderbird email client instance.
SentinelOne, a cybersecurity company, revealed in March that the gang used phoney translation software to target Ukrainians.
GraphSteel and GrimPlant malwares are being disseminated through phishing emails with the subject line “Wage arrears,” typically targeted at those working in government, according to a warning from the Ukrainian national computer emergency response organization CERT-UA. According to CERT-UA, the emails include an attachment called “Wage arrears.xls” that contains reliable statistics and macros.
UNC1151 Operations
Minsk-based Mandiant refers to UNC1151 as a state-sponsored cyber espionage entity that conducts malware campaigns and credential harvesting (see: ‘Ghostwriter’ Disinformation Campaign Targets NATO Allies).
Researchers from Mandiant did not completely rule out Russian participation to either UNC1151 or the Ghostwriter misinformation operation, which is consistent with Russian security interests. However, they were unable to find any proof of any coordination between UNC1151 and Russian advanced persistent threat groups.
The group has been active in Germany and the Baltics, but since the Russian invasion of Ukraine in February, Mandiant says it has turned its attention to Poland and Ukraine.
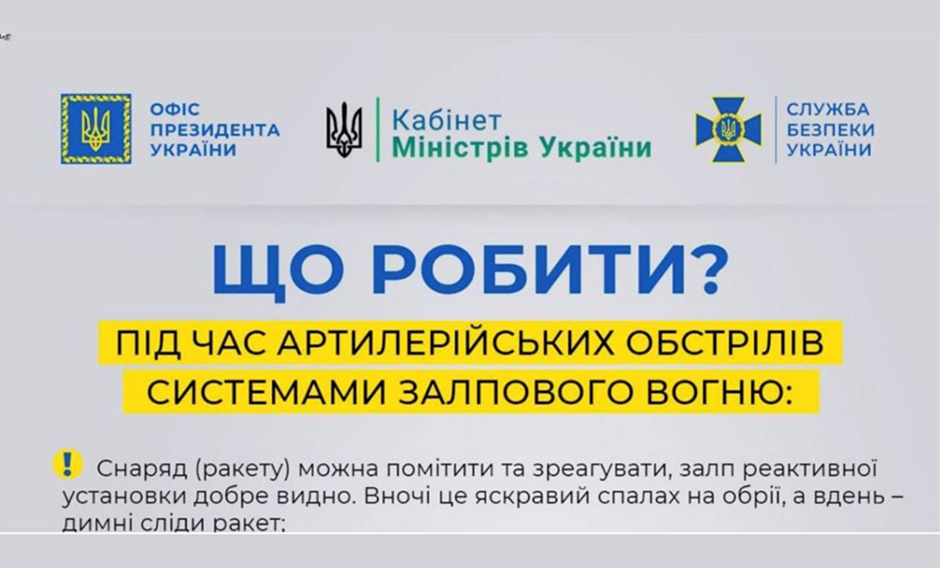
One of its phishing lures contains a message that reads, in English, “Now what? during volley fire systems used for artillery shelling.” Victims that click on the lure have malware called Microbackdoor, a backdoor and command and control tool, infect their machines. This malware has been published on source code repository GitHub since May 2021. It was created by “Cr4sh,” also known as Dmytro Oleksiuk, who also created the BlackEnergy DDoS bot toolkit and other important malware used by Russian threat actor organizations.
Microbackdoor is capable of file uploads and downloads, command execution, updating itself, and screenshotting.
The gang also used malware from the Cobalt Strike framework called Beacon. Executing shell commands, transferring files, running files, and managing files are all among its backdoor commands.
It can also function as a proxy server and record keystrokes and screenshots. “In addition, BEACON may be charged with enumerating systems on a network, port scanning, and harvesting system credentials. Using HTTP or DNS, BEACON talks with a C2 server “Researchers on Mandiant assert.





