Egress, a cybersecurity firm, reports a rise in Phishing attacks imitating LinkedIn emails, and since February, such attacks have increased 232%. The company stated in a report that cybercriminals are using display name spoofing and stylised HTML templates to trick…
Latest posts - Page 71
Hacker group targeting Indian lawyers, activists.
A new hacker group has been tracked to attacks targeting human rights, activists, human rights defenders, academics, and lawyers in India. The attacks attempt to drop “incriminating digital evidence.” Sentinel Group has traced the attacks to a group called “Modified…
Ransomware Attacks: Ways to Win the War Against It
Ransomware is on the rise, but security leaders can fight back by implementing the scope of security’s best approaches for beating the bad guys when it comes to ransomware attacks. 1. Back up organizational data This is the most prominent…
PrivateLoader Malware Distribution Service is Blossoming in PPI Mode
The Pay-Per-Install (PPI) malware service, PrivateLoader, has been acquiring popularity in delivering a motley of malware. Usually, malware operators pay such service owners to get their payloads installed on their targets. PrivateLoader service users According to Intel 471 researchers, PrivateLoader,…
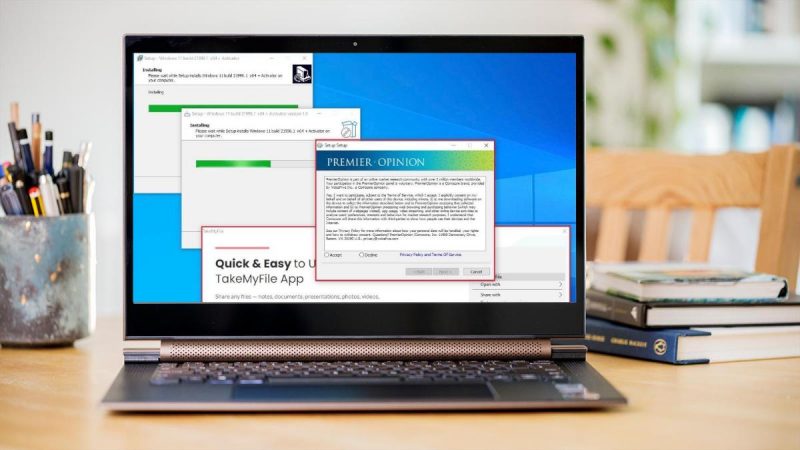
RedLine malware is used by Fake Windows 11 upgrade installers
Threat actors have started dispersing fake Windows 11 upgrade installers to users of Windows 10, tricking them into downloading and running RedLine stealer malware. The timing of the attacks overlaps with the moment that Microsoft announced Windows 11’s broad deployment…
Charming Kitten observed using New backdoor PowerLess
Iran-based Charming Kitten APT has been observed using a new backdoor named PowerLess, along with several other tools. This is a PowerShell-based implant that comes with evasive PowerShell execution. New additions to the arsenal The PowerLess backdoor can download and…
MyloBot used for sending sextortion emails
MyloBot’s latest version has been used to plant malicious payloads, and the payloads are being used to send sextortion emails. The emails have a demand of $2,7321digital currency— for the recipients. MyloBot, first identified in 2018, has a wide range…
U.S, U.K and Australia warn of soaring ransomware attacks
A joint warning has been issued by cybersecurity authorities of Australia, the U.K., and the U.S. The warning concerns rise in advanced, catastrophic ransomware attacks targeting the important infrastructure of organisations globally. The ransomware attacks have targeted various sectors like…
Alert Overload and Handling – A Guide for Lean IT Security Teams
An alarming study revealed the stress and strains that the average cybersecurity team experiences daily. Nearly 70% of teams report feeling emotionally devastated by security alerts. These alerts come at such increased volume, elevated velocity, and high intensity that they…
Samba-Critical Vulnerability Let Attackers Gain Remote Code Execution
A Virtual File System of Samba was found to be vulnerable to Remote Code Execution. Versions before 4.13.17 were vulnerable to this vulnerability. Samba is a software used in SMB (Server Message Block) networking protocol used for file sharing, printer…