“PHP Everywhere” plugin for WordPress, which is used by more than 30,000 websites, has three critical remote code execution (RCE) vulnerabilities. PHP Everywhere, a plugin, allows WordPress admin to use the PHP Everywhere plugin to plant PHP code in pages,…
Latest posts - Page 72
Zimbra issues hotfix for XSS vulnerability under active exploitation
Attackers have targeted mailboxes in multiple waves across two attack phases. Business email platform Zimbra has released a hotfix for a cross-site scripting (XSS) vulnerability whose abuse has underpinned a series of spear-phishing campaigns. A suspected, previously unknown Chinese APT…
Android Users were Targeted by Dark Herring
A fraudulent subscription campaign called Dark Herring has targeted over 100 million Android users worldwide. The campaign has been operating for almost two years. Dark Herring malware was discovered by a research team in Zimperium, who estimated the amount the…
Google auto-enrols users leading to a fall in account hijacking
Since Google announced its campaign to auto-enrol users for 2-step verification last year, Google has auto-enrolled more than 150 million users in 2 step-verification. Google also stated that the auto-enrolment reduced account hijacking. An excerpt from the note, “the number…
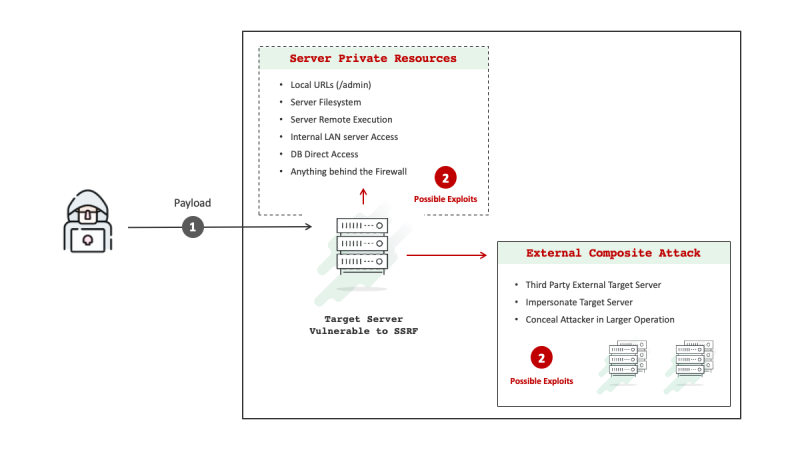
SSRF flaws created in multiple apps via Google Drive integration errors
Execution flaws in Google Drive integrations created server-side request forgery (SSRF) vulnerabilities in a mixture of applications, a security researcher has disclosed. This included Dropbox’s digital signature platform, HelloSign, but “by far the finest” SSRF was completed via CRLF and…
Attackers can Take Over Computers through PowerPoint Files
Attackers use socially engineered emails with .ppam file attachments that hide malware that can rewrite Windows registry settings on targeted machines. The attacker used under-the-radar PowerPoint files to hide malicious executables that can rewrite Windows registry settings to take over…
Indian Government and Military targeted by new CapraRAT Android malware
An advanced persistent threat (APT) group having political ambitions has added a new remote access trojan (RAT) to its malware arsenal. The RAT is an espionage attack targeting Indian military and diplomatic entities. Trend Micro has called the malware CapraRAT;…
Stealthy backdoor used for targeting Taiwanese financial institutions
Taiwanese financial instiutions have been on the radar of a Chinese advanced persistent threat (APT) group. The group has been running a “persistent campaign” targeting Taiwanese financial institutions. The attacks are for espionage; the attacks have planted a backdoor called…
Hackers target European Oil ports
Belgian prosecutors are investigating the hacking of oil facilities in the country’s ports, including Antwerp—Europe’s second-biggest port after Rotterdam. In Germany, prosecutors said they are looking into cyberattacks targeting oil facilities. The ransomware targeting oil facilities locked the systems and…
Threat actor exploiting a zero-day vulnerability in the Zimbra open-source email platform
A threat actor, likely to be Chinese, targeted a zero-day vulnerability in the Zimbra open-source email platform. The zero-day exploitation is part of a spear-phishing program that began in December 2021. Volexity, a cybersecurity company, recorded the espionage operation in…