The Global Cybersecurity Outlook 2022 report has revealed that ransomware attacks have increased as such by 151% in 2021. There were nearly 270 cybersecurity attacks per organization, with each successful security breach costing a company over $3.6 million. According to…
Latest posts - Page 74
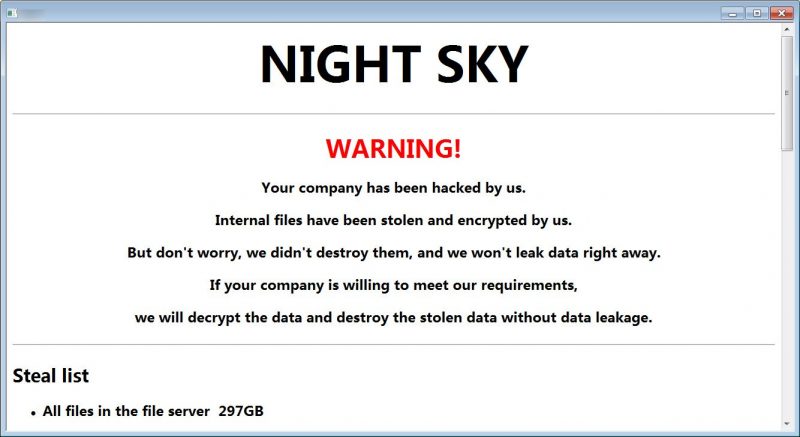
Night Sky, the new ransomware
In the cyber security area, there is new ransomware to keep an eye on called as, ‘Night Sky’. This was first spotted by Malware Hunter Team. It is targeting the corporate networks and is stealing data for extortion from VMware…
Box account’s 2-factor authentication system can be circumvented
Cybersecurity researchers have revealed information on a now-patched bug in Box multi-factor authentication (MFA). The bug could be exploited to circumvent SMS-based login verification. “Using this technique, an attacker could use stolen credentials to compromise an organization’s Box account and…
UniCC the largest dark web market for stolen cards, shuts down
The largest dark web marketplace for stolen credit and debit cards, UniCC has stated that it’s shutting down its operations. Since 2013, UniCC has earned $358 million in purchases entailing cryptocurrencies such as Bitcoin, Litecoin, Ether, and Dash. “Don’t build…
Critical vulnerability in 3 WordPress Plugins impacts 84,000+ websites
Researchers have uncovered a critical vulnerability plaguing three different WordPress plugins. These plugins can affect more than 84,000 websites and may be exploited by threat actors to take over vulnerable websites. “This flaw made it possible for an attacker to…
Rootkit iLO attacking HP Servers – CyberDaily
An unknown rootkit has been targeting Hewlett-Packard Enterprise’s Integrated Lights-Out (iLO) server management technology. The hackers have used the iLO to rig the firmware modules and obliterate data from the infected systems. Amnpardaz, an Iranian cybersecurity firm, uncovered the vulnerability,…
Crypto Mining attacks use evolved version
A crypto mining campaign, which has been active, has developed its method to avoid detection. The threat actors have evolved their attack method to go undetected, new research today has disclosed. The crypto mining attack campaign was first uncovered in…
Log4j news -Log4j patch releases by Apache
Log4j news – On 28th December 2021, another vulnerability affecting the Log4j logging library was discovered. The vulnerability is labelled CVE-2021-44832. The vulnerability CVE-2021-44832 affects versions 2.17.0 and before. The vulnerability was assumed to be patched, but it wasn’t. The…
‘Double Feature’: researchers dived in tool
Cybersecurity researchers have offered insight into a system known as Double Feature. The system tracks different stages of post-exploitation originating from the DanderSpiriz—a full-featured malware framework deployed by the Equation group. DanderSpirtz was first discovered on April 14, 2017; DanderSpritz…
Web application attacks substantial rise
Imperva Research Lab’s study concluded that web application attacks are rising, on average, by 22% each quarter. The study examined nearly 4.7 million web application incidents. Further, the attacks have increasingly increased from Q2 2021 to Q3 2021— a 67.9% surge.…