A threat actor, likely to be Chinese, targeted a zero-day vulnerability in the Zimbra open-source email platform. The zero-day exploitation is part of a…
cybersecurity news
Hackers using a new method to plant AsyncRAT malware
A malware campaign, since September 2021, has been using an advanced phishing attack to deliver the AsyncRAT trojan. “Through a simple email phishing tactic…
Cybersecurity trends in 2022
Every day, new technologies are disrupting and improving our lives, businesses, industries, and in the larger landscape, the conveniences and efficiencies we once thought…
Log4j vulnerability targets SolarWinds, ZyXEL devices
SolarWinds and ZyXEL devices are being attacked by cybercriminals who are searching for Log4jShell vulnerability aka log4j vulnerability. The devices are known to contain…
LastPass Master Passwords are compromised, its users were warned
Some users of the password management app, LastPass, have received very alarming email warnings indicating as someone tried to log into their account from…
Rewind of the 2021 Cybersecurity attacks
The Global Cybersecurity Outlook 2022 report has revealed that ransomware attacks have increased as such by 151% in 2021. There were nearly 270 cybersecurity…
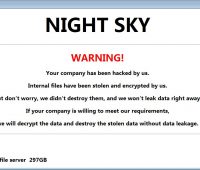
Night Sky, the new ransomware
In the cyber security area, there is new ransomware to keep an eye on called as, ‘Night Sky’. This was first spotted by Malware…
Box account’s 2-factor authentication system can be circumvented
Cybersecurity researchers have revealed information on a now-patched bug in Box multi-factor authentication (MFA). The bug could be exploited to circumvent SMS-based login verification.…
UniCC the largest dark web market for stolen cards, shuts down
The largest dark web marketplace for stolen credit and debit cards, UniCC has stated that it’s shutting down its operations. Since 2013, UniCC has…
Critical vulnerability in 3 WordPress Plugins impacts 84,000+ websites
Researchers have uncovered a critical vulnerability plaguing three different WordPress plugins. These plugins can affect more than 84,000 websites and may be exploited by…