Threat actors have started dispersing fake Windows 11 upgrade installers to users of Windows 10, tricking them into downloading and running RedLine stealer malware.…
cybersecurity news
Charming Kitten observed using New backdoor PowerLess
Iran-based Charming Kitten APT has been observed using a new backdoor named PowerLess, along with several other tools. This is a PowerShell-based implant that…
U.S, U.K and Australia warn of soaring ransomware attacks
A joint warning has been issued by cybersecurity authorities of Australia, the U.K., and the U.S. The warning concerns rise in advanced, catastrophic ransomware…
Alert Overload and Handling – A Guide for Lean IT Security Teams
An alarming study revealed the stress and strains that the average cybersecurity team experiences daily. Nearly 70% of teams report feeling emotionally devastated by…
Samba-Critical Vulnerability Let Attackers Gain Remote Code Execution
A Virtual File System of Samba was found to be vulnerable to Remote Code Execution. Versions before 4.13.17 were vulnerable to this vulnerability. Samba…
Many WordPress sites have become vulnerable as PHP RCE vulnerability identified
“PHP Everywhere” plugin for WordPress, which is used by more than 30,000 websites, has three critical remote code execution (RCE) vulnerabilities. PHP Everywhere, a…
Zimbra issues hotfix for XSS vulnerability under active exploitation
Attackers have targeted mailboxes in multiple waves across two attack phases. Business email platform Zimbra has released a hotfix for a cross-site scripting (XSS)…
Android Users were Targeted by Dark Herring
A fraudulent subscription campaign called Dark Herring has targeted over 100 million Android users worldwide. The campaign has been operating for almost two years.…
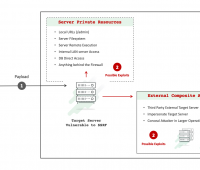
SSRF flaws created in multiple apps via Google Drive integration errors
Execution flaws in Google Drive integrations created server-side request forgery (SSRF) vulnerabilities in a mixture of applications, a security researcher has disclosed. This included…
Attackers can Take Over Computers through PowerPoint Files
Attackers use socially engineered emails with .ppam file attachments that hide malware that can rewrite Windows registry settings on targeted machines. The attacker used…