Cybersecurity experts have issued a warning over “huge phishing efforts” that disseminate five different types of malware and target Indian banking users. New, Large-Scale Malicious Campaigns Targeting Customers of Top Indian Banks.
In a study released this week, Trend Micro stated that “the bank customers targeted include account subscribers of seven institutions, including some of the most well-known banks situated in the country and potentially affecting millions of users”.
The banks targeted include, Axis Bank, ICICI Bank, and the State Bank of India (SBI), among others. New, Large-Scale Malicious Campaigns Targeting Customers of Top Indian Banks.
The entry point for all infection chains is SMS messages with phishing links that entice potential victims to enter their personal information and credit card information in order to purportedly receive a tax refund or earn credit card reward points.
The smishing attacks, which spread Elibomi, FakeReward, AxBanker, IcRAT, and IcSpy, are merely the most recent in a string of rewards-themed malware campaigns that Microsoft, Cyble, and K7 Labs have identified over the past year.
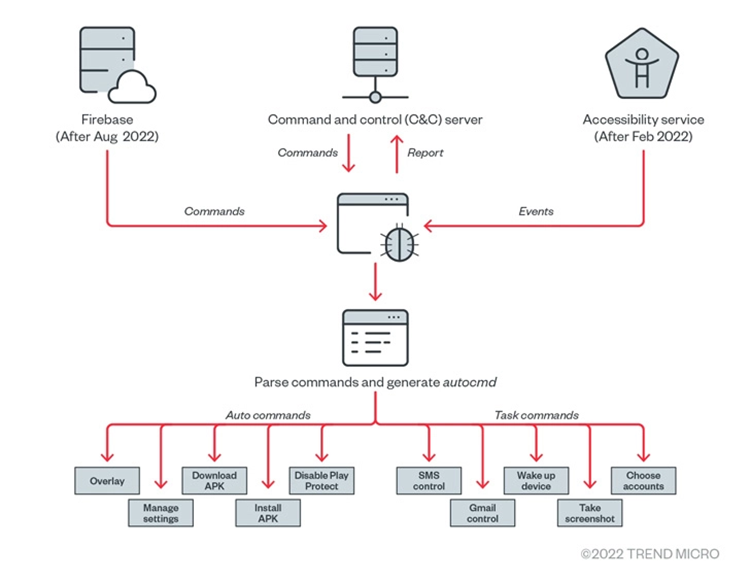
Elibomi, which McAfee first identified in September 2021, exploits Android’s accessibility API rights to take over infected smartphones. And designed to collect personal information, take screenshots, and even record the lock screen code or pattern.
The Malware
The mobile malware has undergone multiple updates, and a new Elibomi variation known as Drinik. Drinik targeted consumers of 18 different banks by pretending to be the Income Tax Department of India.
Instead of using an overlay on other apps like bank applications to steal users’ credentials, Elibomi instals an overlay by adding a view to the current window, according to the researchers.
Similar to this, after being installed, the banking trojans FakeReward and AxBanker ask the victim for permission to read SMSes and notifications. And subsequently used to exfiltrate incoming SMS messages. AxBanker also shows bogus pages to steal credit card data.
In order to increase the chance of a successful attack and persuade the user to download the malicious app in order to receive “instant reward points,” the apps themselves are distributed through phishing websites with domain names that are similar to those of their legitimate counterparts.
The Conclusion
Despite the similarities in themes involving stolen data and phishing, Trend Micro claimed that there is no hard evidence linking all of these malware families to a single threat actor.
While these malware families haven’t targeted any other consumers outside of India, phishing campaigns there have considerably expanded and are getting better at avoiding detection, according to Trend Micro.
“A growing number of new threat actors are entering the India underground market, bringing with them lucrative business models, and interacting with other malicious players to learn from, exchange ideas with, and establish connections,” according to one theory for the increase.





