Threat actors encrypt Windows PCs by breaking into publicly available Remote Desktop services using the relatively new Venus Ransomware.
Venus Ransomware has since encrypted victims all across the world and looks to have started operating in the middle of August 2022. Although it is unknown if they are connected, another ransomware has been utilizing the same encrypted file extension since 2021.
Security expert linuxct contacted MalwareHunterTeam in order to get information on the ransomware, who then informed.
According to Linuxct, the threat actors used the Windows Remote Desktop protocol to reach a victim’s corporate network.
RDP was reportedly used for the first network access by another victim in the BleepingComputer forums. Even while the service was running on a non-standard port number.
How Windows devices are encrypted by Venus
When activated, the Venus ransomware would make an effort to kill 39 processes linked to Microsoft Office and database servers.
The following command is used by the ransomware to erase event logs, disable Data Execution Prevention, and destroy Shadow Copy Volumes:
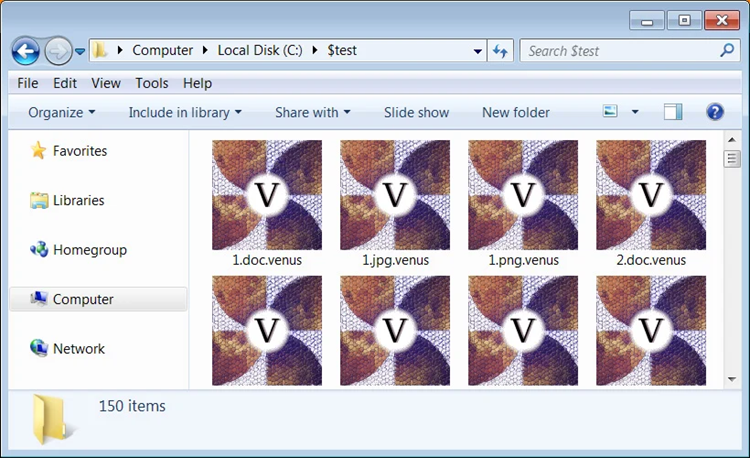
The ransomware will add the.venus extension to encrypted files, as demonstrated below. For instance, test.jpg would be renamed test.jpg after being encrypted. Venus.
The ransomware will append a “goodgamer” filemarker and other data to the end of each encrypted file. At this point, it is unknown what this further data entails.
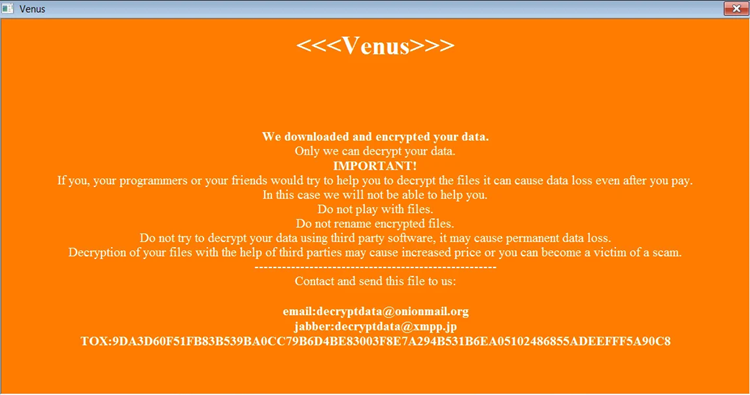
When the device has been fully encrypted, the ransomware will produce an HTA ransom notice in the %Temp% folder, which will be automatically displayed.
This ransomware, which goes by the name “Venus,” has shared a TOX address and email address that may be used to get in touch with the attacker. And discuss a ransom payment, as you can see below. A base64 encoded blob, which is probably the encrypted decryption key, can be found at the end of the ransom note.
The Venus ransomware is now comparatively active, with fresh submissions being published to ID Ransomware on a daily basis.
It is essential to hide these services behind a firewall because the ransomware appears to be targeting publicly exposed Remote Desktop services, even those using irregular TCP ports.
No Remote Desktop Services should ideally be openly accessible on the Internet and only available over a VPN.





