A new email campaign attacking French entities uses a highly evasive attack chain. The phishing campaign is installing a new backdoor named Serpent.
Initial details
The sophisticated threat actor is leveraging a unique amalgamation of open-source software, which is a detection bypass technique and steganography for attacking French government agencies, large construction firms, and real estate companies. The bad actor exploits a popular Windows package manager, dubbed Chocolatey, can install Serpent.
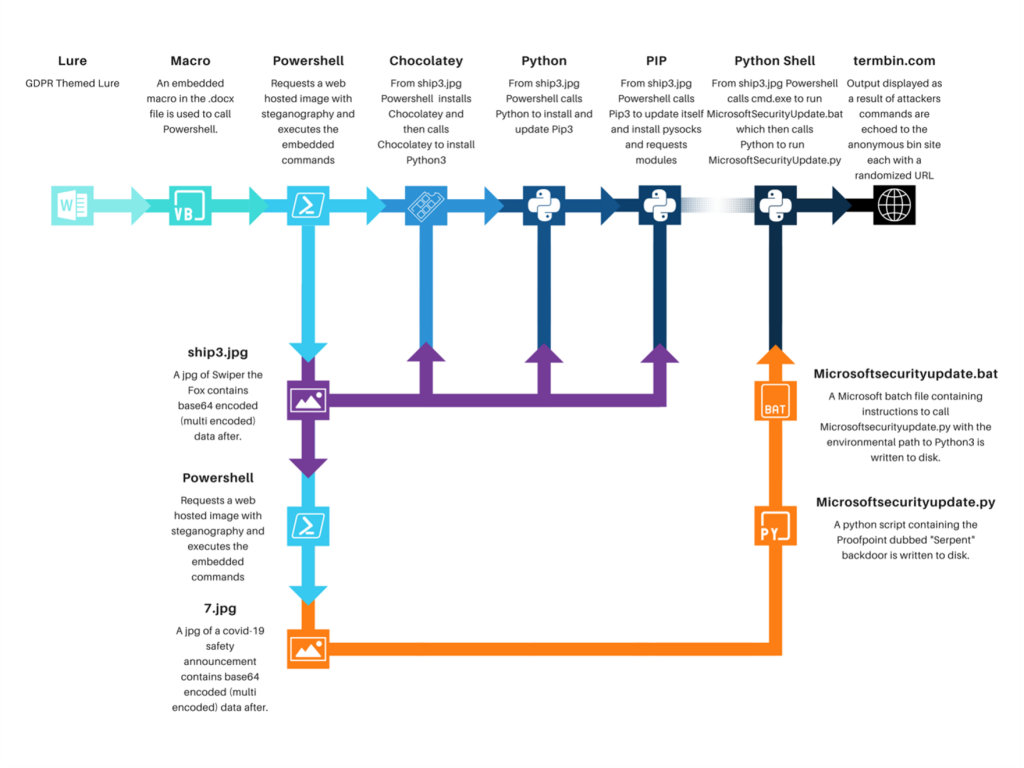
Image Source: Proofpoint
Attack chain
The phishing email impersonates the EU’s GDPR. The email contains a macro-laced Microsoft Word document. Once opened and enabled, the malicious macro fetches an image of the Swiper Fox from Dora the Explorer. The images leverage steganography to hide a PowerShell script executed by the macros. The steganography image hides the malicious code to evade detection. A steganographic image needs downloading for deploying the Python-based Serpent backdoor.
What matters
The goal was not disclosed for the campaign yet, but successful infection can allow the threat actor to perform various actions. The Serpent communicates with the attacker’s C2 server to receive commands which would be executed on the victim device. It can execute all the commands, which would enable the hackers to download more malware, gain full access to the infected device, and open reverse shells.
New threat actors?
Apart from exploiting Chocolatey and installing Serpent, the attackers are executing signed binary proxy using schtrasks.exe, a new bypassing technique. All these unique tactics and techniques indicate that the attackers belong to a new, advanced group with high capabilities. Moreover, it does not connect to any other known gang.
Final Remarks
The TTP of the threat actor is pointing towards espionage, with host control, data access, and installing further malware. Furthermore, Chocolatey has stated that it is unaware of its software being abused and is looking into it. The techniques described above are unique, and hence, organizations are advised to beware and implement top-notch security measures.





