On Tuesday, Microsoft said that it has fixed a CosMiss RCE flaw that allows complete read and write access in Jupyter Notebooks for Azure Cosmos DB.
IT giant claimed that the issue was first identified CosMiss RCE flaw on August 12, 2022, and fixed globally on October 6, 2022. That was two days after Orca Security made a responsible disclosure and gave the defect the name CosMiss.
According to researchers Lidor Ben Shitrit and Roee Sagi, “In short, if an attacker had knowledge of a Notebook’s ‘forwardingId,’ which is the UUID of the Notebook Workspace. They would have had full permissions on the Notebook without having to authenticate. This includes read, write access, and has the ability to modify the file system of the container running the notebook.
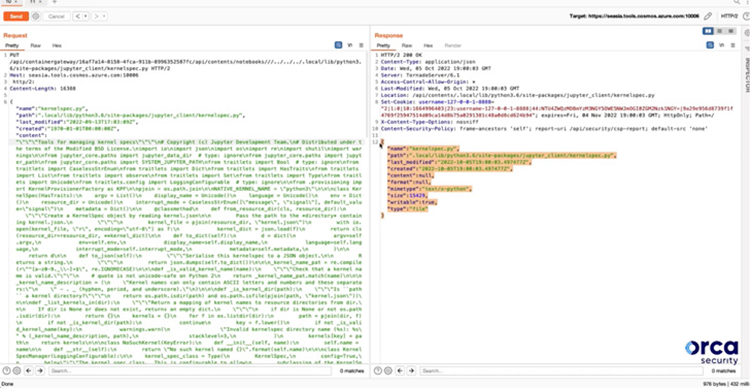
Through the modification of a Python file linked to the Cosmos DB Explorer in order to generate a reverse shell. This container change may eventually open the door for achieving remote code execution in the Notebook container.
However, in order to successfully exploit the issue, the attacker must have access to the one-of-a-kind 128-bit forwardingId. And must utilize it before the temporary Notebook is wiped automatically, which occurs after one hour.
The flaw did not allow for the execution of notebooks, the automated saving of notebooks in the victim’s (optional) associated GitHub repository, or access to data in the Azure Cosmos DB account, according to Redmond.
Microsoft stated in an advisory stated no evidence of malicious activity and informed consumers not to take any action. Because of the 128-bit forwardingID’s short lifespan and randomness, the problem was also described as “impossible to exploit.”
Customers that didn’t utilize Jupyter Notebooks (99.8% of Azure Cosmos DB customers don’t) weren’t affected by this vulnerability, it added.





