Customers of Google Fi, the company’s U.S.-only mobile internet and telecoms service, have been notified that a data breach at one of its primary network providers may have exposed personal information.
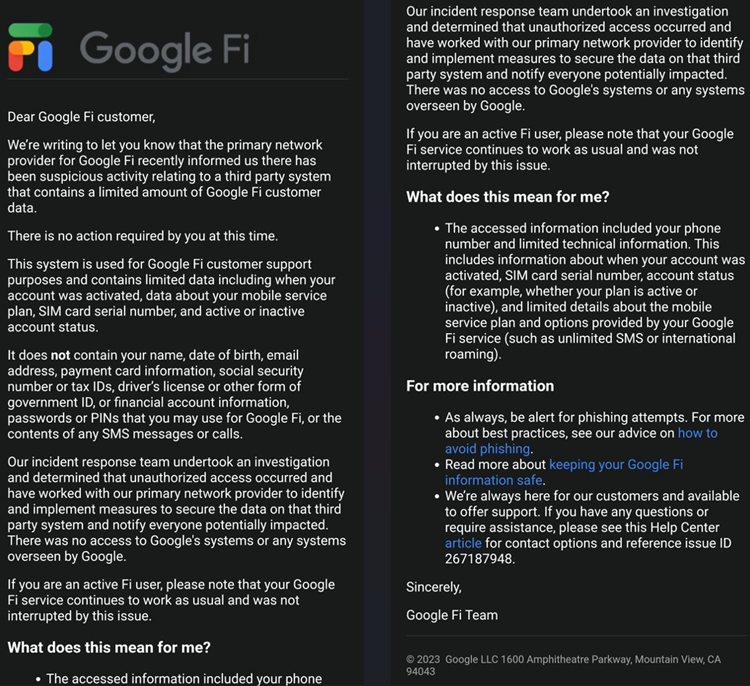
Customers of Google Fi received notifications from Google this week that their contact information, SIM card serial numbers, account status (active or passive), account opening date, and information about mobile service plans had been compromised.
Google clarified that the compromised systems did not contain sensitive information. Such as complete names, email addresses, credit card numbers, SSNs, tax identification numbers, government identification numbers, account passwords, phone contents, or SMS messages.
Customers are informed, “our incident response team underwent an investigation and determined that unauthorized access occurred. Also have started working with our main network provider to develop and implement metrics to safeguard the information on that 3rd party political system and notify everybody potentially impacted.”
“Neither Google’s systems nor any systems under Google’s control were accessible.”
Although Google has not disclosed the compromised primary network provider’s identity, It is assumed that they’re referring to T-Mobile.
Also, read Google Play – Shady reward apps went over 20 million downloads.
T-Mobile informed that, in November 2022, an API data breach exposed the personal data of about 37 million members.
Google should check whether this is connected to the T-Mobile breach, its yet to clarify.
Data breaches led to SIM swap attacks.
Unfortunately, threat actors were able to carry out SIM swap attacks on some Google Fi users due to the leaked technical SIM data. One customer even claimed that the hackers had accessed their Authy MFA account.
Also, read Hackers steal info by spreading malware through Google search ads.
Threat actors use SIM swapping attacks to get cellphone companies to port a customer’s mobile number to a SIM card they control.
The threat actor assumes the victim’s identity through social engineering in these assaults. The numbers are ported to a different device for some reason. They supply sensitive personal information that could be used in phishing scams. And data breaches to persuade the cellphone provider that they are the customer.
Contacting a mobile customer care agent would have been much easier if the Google Fi data breach had included phone numbers. These are easily linked to a client’s identity and the serial number of SIM cards.
Once the number has been moved, threat actors will access the perpetrator’s text messages, particularly MFA codes. This allows them to access online accounts or take control of services that use a person’s phone number as a security measure.
Customers who had experienced SIM swap assaults received a separate message from Google informing them that the attackers had temporarily been able to migrate their phone numbers to another SIM. Users’ voicemails weren’t compromised, though.
“On January 1, 2023, your phone service was switched from your SIM card to another SIM card for approximately 1 hour 48 minutes. The illegal access during this temporary transfer may have included using your phone number to make and receive texts and calls. Your mail may have yet to be accessed despite the SIM transfer. Your SIM card’s Google Fi service has been restored. A: Google.
Proof of SIM Swap
One victim of the SIM-swapping attacks posted about his experience on Reddit, describing how his email and finances. Authy authentication server app accounts were all taken over in real time.
Since they could read my SMSes and circumvent SMS-based 2-fac. The hacker utilized this to gain control of three of my internet accounts—my primary email, an income statement, and the Authy authenticator app.
Once a two-factor authentication scheme app is taken over, it is much simpler for hackers to access other accounts. Mainly if they were created with a phone number as the registration method.
He claims that notwithstanding his efforts to halt it by alerting Google Fi, customer service disregarded him.








