Through search results for a pirated edition of the CCleaner Pro Windows optimization tool, malware that steals your passwords, credit cards, and crypto wallets is being marketed.
This new malware distribution effort, called “FakeCrack,” was uncovered by Avast analysts, who say their customer telemetry data shows an average of 10,000 infection attempts every day. France, Brazil, Indonesia, and India account for the majority of the victims.
This campaign’s virus is a formidable data thief that can gather personal information and bitcoin assets while also routing internet traffic through data-snatching proxies.
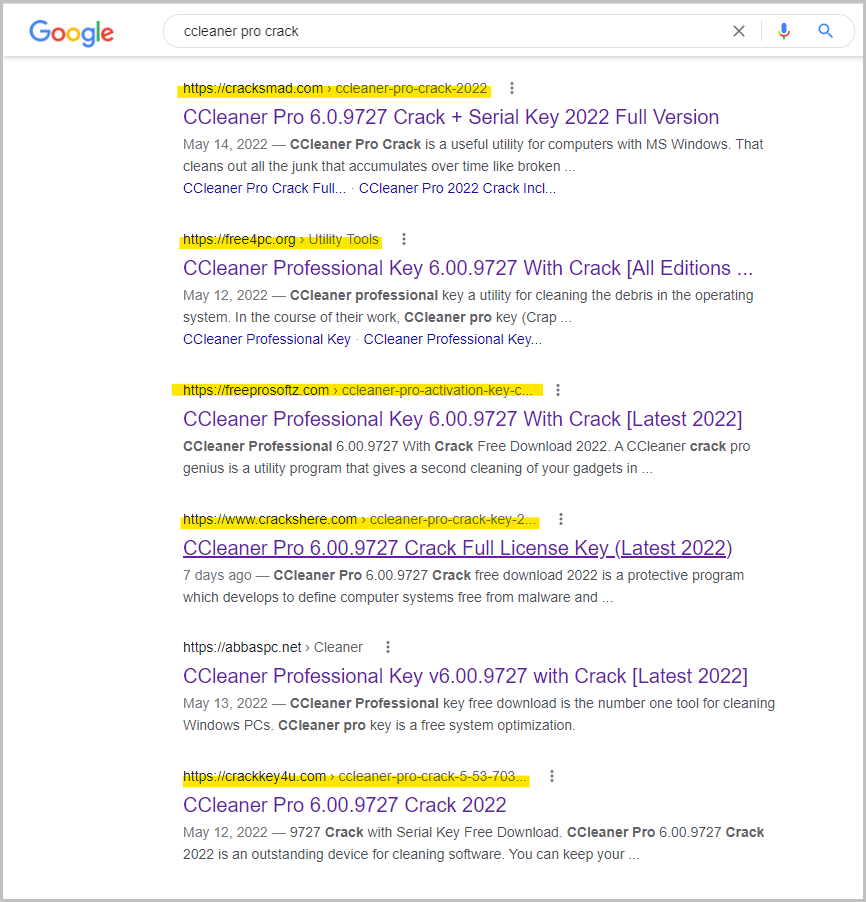
A Black Hat SEO campaign
To get more individuals to download tainted executables, the threat actors use Black Hat SEO strategies to position their malware-distribution websites high in Google Search results.
Avast discovered a cracked version of CCleaner Professional, a popular Windows system cleanser and performance optimizer that many users still consider a “must-have” programme.
The poisoned search results lead the victim to a series of websites that eventually lead to a landing page with a ZIP file download option. A reputable file hosting site, such as filesend.jp or mediafire.com, is frequently used to host this landing page.
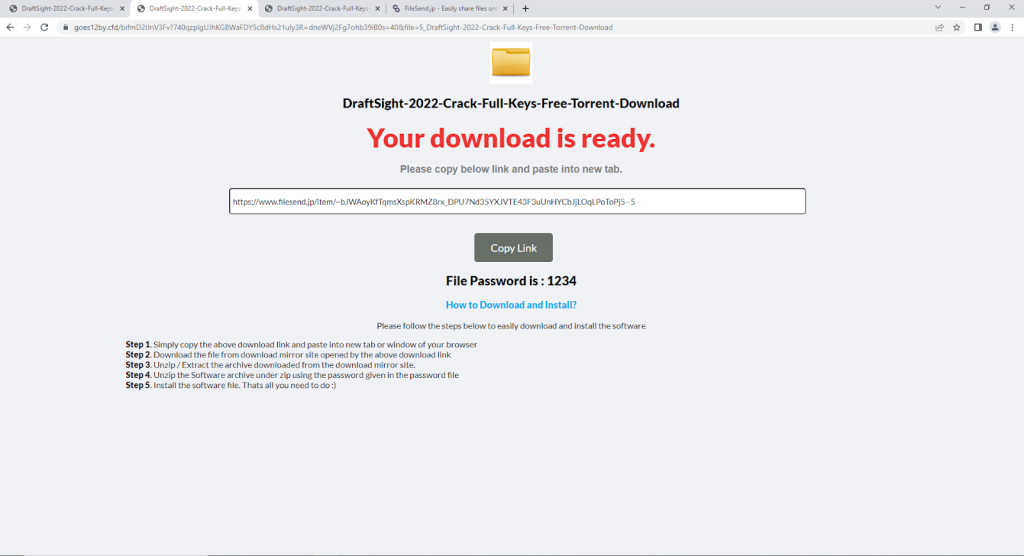
The ZIP is password-protected with a weak PIN like “1234”, which is only there to keep anti-virus software from detecting the payload.
Typically, the programme inside the archive is named “setup.exe” or “cracksetup.exe,” although Avast has spotted eight different executables used in this operation.
A dangerous info-stealing malware
In order to steal information stored in online browsers, such as account passwords, saved credit cards, and cryptocurrency wallet credentials, malware victims are deceived into installing efforts to steal information.
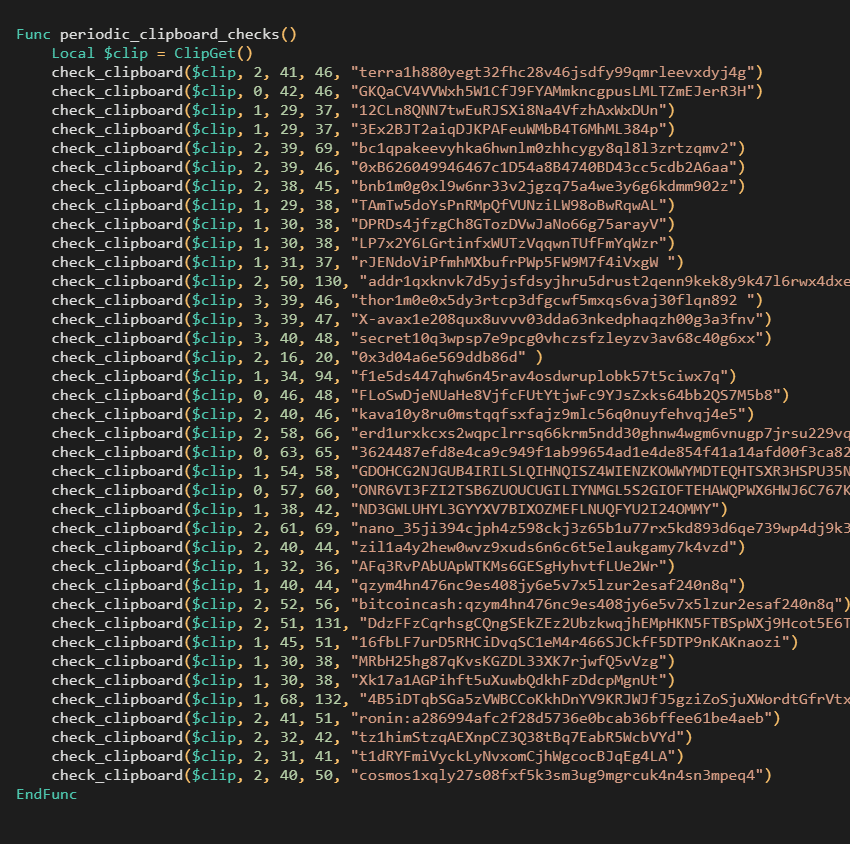
It also looks for copied wallet addresses on the clipboard and substitutes them with ones controlled by the malware’s controllers in order to reroute funds. This clipboard hijacking tool works with Bitcoin, Ethereum, Cardano, Terra, Nano, Ronin, and Bitcoin Cash addresses, among others.
The infection also use proxies to steal cryptocurrency market account credentials using a man-in-the-middle attack that is difficult to detect or recognise by the victim.
In the study, Avast outlines how attackers were able to set up an IP address to download a malicious Proxy Auto-Configuration script (PAC).
“By entering this IP address into the system, all traffic from the victim to any of the mentioned websites is routed to a proxy server controlled by the attacker.”
A new registry key in “HKCUSoftwareMicrosoftWindowsCurrentVersionInternet Settings” adds this proxying technique.
It can be turned off by going to Network & internet in Windows Settings and turning off the “Use a proxy server” option.
Because the campaign is already well-established and infection rates are high, avoid downloading cracked software from any source, even if the download sites appear to be highly ranked on Google.









