
An Android spyware application was discovered that poses a “Process Manager” service to capture sensitive data from afflicted devices.
The software, which has the package name “com.remote.app,” establishes communication with a remote command-and-control server, 82.146.35[.]240, which was previously recognized as infrastructure belonging to the Turla hacking gang located in Russia.
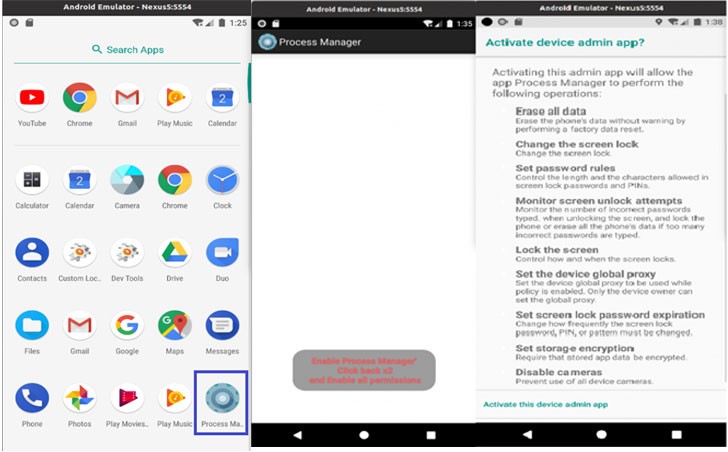
“A warning displays when the application is executed concerning the rights granted to the application,” Lab52 researchers noted. “These include screen unlock attempts, locking the screen, setting the device’s global proxy, setting screen lock password expiration, encrypting storage, and disabling cameras.”
Once “activated,” the virus hides its gear-shaped icon on the home screen and works in the background. It exploits the application’s broad capabilities to access the device’s contacts and call history, track its location, send and read messages, access external storage, snap images, and record audio.
The information gathered is saved in JSON format and then sent to the remote server specified earlier. Despite using the same C2 server, Lab52 claims it doesn’t have enough evidence to link the malware to the Turla organization. The actual initial access vector used for delivering the malware and the campaign’s intended targets are also unknown.
However, the rogue Android software also tries to download a legitimate app called Roz Dhan (Hindi for “Daily Wealth”), which has over 10 million downloads and allows users to earn cash incentives by completing surveys and quizzes.
“The program is available on Google Play and is used to earn money,” the researchers explained that this includes a referral mechanism, which the malware misuses, and the attacker makes a profit by installing it on the device.
Source: https://thehackernews.com/2022/04/researchers-uncover-new-android-spyware.html









