
The weekend saw a malware attack on SHI International’s network, a New Jersey-based supplier of information technology (IT) goods and services.
With $12.3 billion in projected revenue for 2021 and 5,000 workers worldwide working out of operational hubs in the United States, the United Kingdom, and the Netherlands, SHI positions itself as one of North America’s biggest providers of IT solutions.
Furthermore, it claims to serve more than 15,000 corporate, enterprise, public sector, and academic customer groups globally.
SHI released a statement saying that it was the subject of a planned and expert malware attack over the Fourth of July vacation weekend.
“The incident was immediately recognised and measures were enacted to minimise the damage on SHI’s systems and operations,” according to the statement from the security and IT teams at SHI.
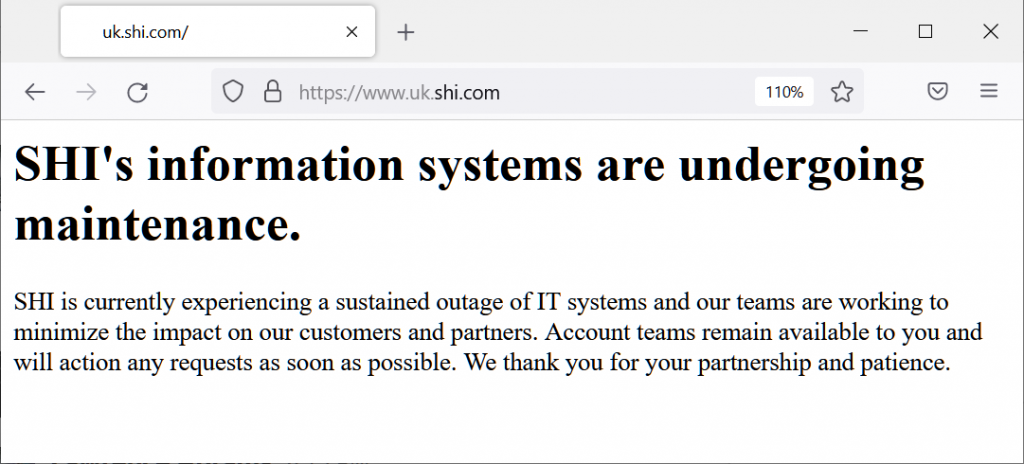
Following the incident, SHI updated its website with a notice informing users that maintenance was being done on its information systems because of a “continuous outage.”
The malware attack statement that was posted on the business blog afterwards took the place of this message.
In addition to returning Amazon CloudFront/S3 SHI problems since the attack, some website pages did so up until the time this report was published.
SHI was compelled to take several of its systems offline, including the business’s public websites and email, while assessing the integrity of its systems and looking into the security incident.
All email servers that had been shut down following the incident were restarted by SHI staff members beginning on Wednesday morning.
Access to additional compromised systems on the network is also being worked on by the company’s IT specialists.
There is no evidence to suggest that client data was exfiltrated during the attack, the business continued. “The investigation into the issue is ongoing, and SHI is collaborating with federal organisations including the FBI and CISA,” it said.
Additionally, SHI stated that it will keep customers informed at every stage of the procedure and that the malware assault had no impact on any external systems that were part of its supply chain.
An SHI representative provided a link to the statement posted on the company’s blog in response to BleepingComputer’s earlier request for more information.
References: https://www.bleepingcomputer.com/news/security/it-services-giant-shi-hit-by-professional-malware-attack/





