Threat actors can now avoid some of the most powerful phishing defences thanks to a new hacking approach. Criminal organizations are using a new technique for phishing attacks that might render threat actors undetectable, according to security researchers.
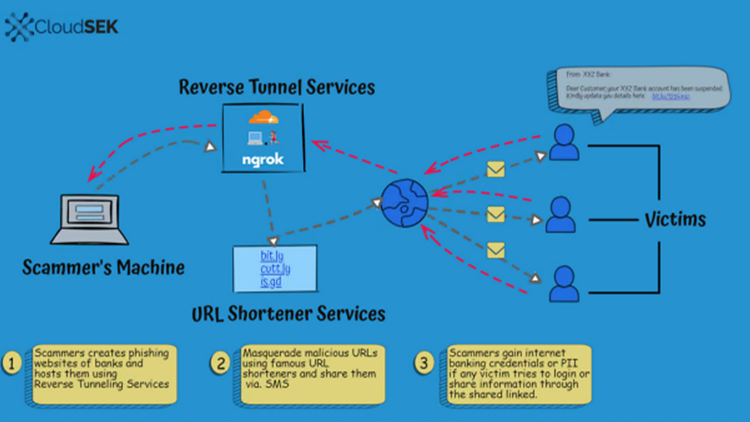
The method entails leveraging URL shorteners and “reverse tunnel” services to launch massive phishing campaigns. Additionally, the groups employing these methods leave no traces.
Instead, threat actors can host phishing pages on random URLs using their local computers. These can aid in avoiding URL scanning services’ detection. Using URL shortener services, the gangs can further conceal their identity.
Down the hole
Technically speaking, the attackers are not taking advantage of a weakness. Instead, they are abusing commercially available, genuine services to get beyond anti-phishing safeguards. The method uses Bit.ly, Ngrok, and Cloudflare’s Argo Tunnel as supporting services.
Security researchers at CloudSEK discovered the strategy that targets consumers of Indian banks when they discovered the threat.
Here, phishing attacks sought to trick users into disclosing their financial information, Aadhaar (India’s national identifying number), and other private data.
According to Darshit Ashara, a lead threat researcher at CloudSEK, we found it while we were monitoring the internet for our client-related assets, impersonations, and data.
“We began seeing patterns of such misuse of several reverse tunnel providers throughout the ordinary course of our investigation.”
Although the approach was employed in the US, the UK, and Europe, CloudSEK discovered attempts against Indian bank consumers. Ashara continued, “Reverse tunnel attacks have increased in frequency recently.
Threat actors who employ reverse tunneling frequently distribute SMS-based spam with phishing URLs. They shorten the URLs using well-known URL shortening providers.
“We have seen this approach employed to target the majority of significant businesses and organizations.”
Hiding in the shadows
Criminal organizations can avoid some of the most potent defenses by using reverse tunnels.
Because of their dependency on hosting firms and their use of domains that impersonate targeted companies or phrases. According to CloudSEK, it is possible to identify phishing groups.
Hosting companies will take down the fake names even if there is insufficient proof for law authorities to pursue the phishing gangs.
The attackers have some protection if they use names with “random or generic” keywords because they can’t be accused of trademark infringement. However, hackers can totally avoid hosting by keeping the phishing binaries on just a local PC thanks to reverse tunnels.
It becomes even more difficult to track the attack when URL shortening is added, which increases the likelihood that victims would fall for the hoaxes. Attribution and prosecution are made much more difficult by the fact that the majority of reverse tunnel URLs are transient, and frequently active for just 24 hours.
Improved Monitoring
CloudSEK demands improved monitoring of reverse tunnel services.
For instance, Ngrok now requests users’ IP addresses and registration information before allowing them to host HTML content. In contrast to Cloudflare’s account creation requirement.
Since there is no actual malicious activity with URL shortening—they merely direct consumers to a website—it is more difficult to control.
However, CloudSEK acknowledges that identifying assaults requires outside monitoring. Therefore, targeted businesses may need to rely on user education to combat this attack vector.
The crucial distinction is attribution, according to Chris Preece, head of cyber operations at digital risk management company Protection Group International. “Effectively, this is another avenue for phishing attacks,” he added.
If a domain is registered with a hosting company, then the hosting company can respond to complaints and take down a website. But, with reverse tunnels, the provider of the reverse tunnel has no responsibility for it. This makes the website potentially more difficult to take down.
When used with a URL shortener, it can be extremely powerful. For reducing clicking on a fraudulent link, we have the cliched suggestion to increase phishing knowledge.





