Volodymyr “Bob” Diachenko, a cybersecurity expert from Ukraine and the creator of SecurityDiscovery.com, discovered two IP addresses on August 2 that were home to enormous volumes of very sensitive data belonging to Indian residents.
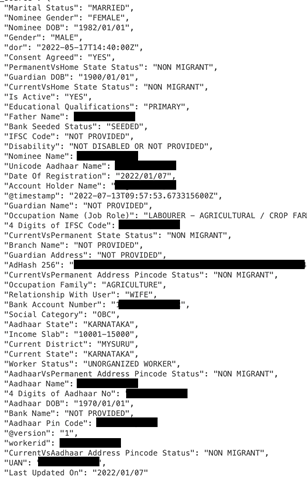
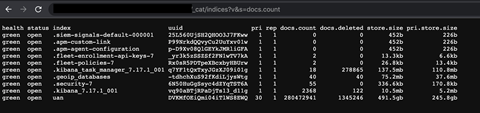
There were 8,390,524 records on one IP, while there were 280,472,941 records on the other. According to a screenshot posted by Diachenko, the compromised data included, among other things, names and addresses, Universal Account Numbers (UANs), bank account numbers and IFSC codes, Aadhaar card numbers, employment information, income brackets, marital status, and names and personal details of guardians.
The data is authentic, according to a sample that Diachenko sent ETCISO from the compromised database. Entering the IFSC code and account number in the ‘Send Money to Bank A/C’ area on Paytm or GPay is a preliminary test to determine the validity of the data. The entire name of the account holder will automatically populate if the account information is accurate. Three accounts were chosen at random for verification, and we found that all three of the names that auto-populated matched the data from the stolen database.
The researcher’s statement that, as far as he is aware, the leaked database hasn’t been offered for sale on an online marketplace or a hacker forum on the dark web, which is frequently the case when sizable databases containing users’ sensitive information are compromised, provides a small amount of comfort. When SecurityDiscovery’s systems identified the two IPs with passwordless Elasticsearch clusters – an open source analytics solution – including indices labeled “UAN,” the data breach and its significance were discovered. As we all know, the Employees’ Provident Fund Organization issues each citizen with a unique 12-digit number known as a UAN (EPFO). Diachenko has sent letters to the EPFO and CERT-in but hasn’t heard back yet. No acknowledgment of the occurrence has been made.
What we know about the data leak
According to Diachenko, both IP addresses were based in India and hosted on Azure. Reverse DNS analysis, which is frequently done to identify a specific domain or hostname for an IP address, was performed but came up empty.
Due to this, there is currently no information accessible regarding the attack vector utilized or how the hackers gained access to and leaked the data.
The affected IPs were originally identified on August 1 by Shodan and Censys, the two search engines SecurityDiscovery utilizes to look for data breach occurrences around the world. However, it is impossible to say for how long the two IPs were left open to the internet. The information request from ETCISO hasn’t received a response from EPFO yet.
How serious is the data breach?
The available evidence suggests that the data leak is highly significant. While PII like full names, addresses, dates of birth, Aadhaar numbers, etc., is a tool in the hands of cybercriminals who exploit it for spear-phishing attacks, highly sensitive information like UANs, annual income, bank account data, and income slabs is not.
Troy Hunt, a Queensland resident and founder of the data breach search website Haveibeenpwned, explains to ETCISO: “The quantity and the range of data in the sample record are both noteworthy if this information is reliable. Given such circumstances, this is a significant breach.” The seriousness and scope of the data breach have also been confirmed by Indian cybersecurity specialists and professionals with whom Diachenko talked.
Diachenko reported the event to CERT-in and EPFO, but he hasn’t heard anything from them. However, their quick response to the researcher’s tweets suggests how severe the Incident was given their quick action. “Given the size and clear importance of the data, I chose to tweet about it without mentioning the source or any other relevant information. Both IP addresses were taken down and are currently unreachable within a day of my tweet, according to Diachenko.
EPFO faces the second cyberattack in four years
The situation that happened today is not EPFO’s first run-in with cyberattacks. The Aadhaar-seeding portal was suspended in May 2018 as a result of security flaws.
In the 2018 event, the EPFO didn’t raise the alarm until the Information Bureau did so. In a statement to The Indian Express, the group said that neither its servers nor software were to blame for the data leak.
According to the EPFO, the event was caused by a leak in CSC e-Government Services India Ltd. Software. In response to the accusation, the CSC placed the onus back on the EPFO, claiming that hackers had taken advantage of security vulnerabilities and backdoor shells on the latter’s website.
Data breach? What data breach?!
Even though it is required that corporations notify CERT of breach incidences, it is not unusual for impacted companies to deny a breach even when presented with concrete evidence. Troy Hunt, a cybersecurity researcher, consultant, and founder of the Haveibeenpwned data breach search website, makes the following observation to ETCISO: “The issue with attribution is that even when a company’s data has actually been compromised (and I have high confidence in its authenticity), businesses frequently deny it. It happens far too often.”





